This browser is no longer supported.
Upgrade to Microsoft Edge to take advantage of the latest features, security updates, and technical support.

Microsoft Intune securely manages identities, manages apps, and manages devices
- 15 contributors
As organizations support hybrid and remote workforces, they're challenged with managing the different devices that access organization resources. Employees and students need to collaborate, work from anywhere, and securely access and connect to these resources. Admins need to protect organization data, manage end user access, and support users from wherever they work.
To help with these challenges and tasks, use Microsoft Intune .

Microsoft Intune is a cloud-based endpoint management solution. It manages user access to organizational resources and simplifies app and device management across your many devices, including mobile devices, desktop computers, and virtual endpoints.
You can protect access and data on organization-owned and users personal devices. And, Intune has compliance and reporting features that support the Zero Trust security model .
This article lists some features and benefits of Microsoft Intune.
- To get Intune, go to Licenses available for Microsoft Intune and Intune 30-day trial .
- For information on what it means to be cloud-native, go to Learn more about cloud-native endpoints .
Key features and benefits
Some key features and benefits of Intune include:
You can manage users and devices , including devices owned by your organization and personally owned devices. Microsoft Intune supports Android, Android Open Source Project (AOSP), iOS/iPadOS, Linux Ubuntu Desktop, macOS, and Windows client devices. With Intune, you can use these devices to securely access organization resources with policies you create.
For more information, go to:
- Manage identities using Microsoft Intune
- Manage devices using Microsoft Intune
- Supported operating systems in Microsoft Intune
If you manage on-premises Windows Server, you can use Configuration Manager.
Intune simplifies app management with a built-in app experience, including app deployment, updates, and removal. You can connect to and distribute apps from your private app stores, enable Microsoft 365 apps, deploy Win32 apps, create app protection policies, and manage access to apps & their data.
For more information, go to Manage apps using Microsoft Intune .
Intune automates policy deployment for apps, security, device configuration, compliance, conditional access, and more. When the policies are ready, you can deploy these policies to your user groups and device groups. To receive these policies, the devices only need internet access.
Employees and students can use the self-service features in the Company Portal app to reset a PIN/password, install apps, join groups, and more. You can customize the Company Portal app to help reduce support calls.
For more information, go to Configure the Intune Company Portal apps, Company Portal website, and Intune app .
Intune integrates with mobile threat defense services, including Microsoft Defender for Endpoint and third party partner services. With these services, the focus is on endpoint security and you can create policies that respond to threats, do real-time risk analysis, and automate remediation.
For more information, go to Mobile Threat Defense integration with Intune .
You use a web-based admin center that focuses on endpoint management, including data-driven reporting. Admins can sign into the Intune admin center from any device that has internet access.
For more information, go to Walkthrough the Intune admin center . To sign in to the admin center, go to Microsoft Intune admin center .
This admin center uses Microsoft Graph REST APIs to programmatically access the Intune service. Every action in the admin center is a Microsoft Graph call. If you're not familiar with Graph, and want to learn more, go to Graph integrates with Microsoft Intune .
The Microsoft Intune Suite offers advanced endpoint management and security . The suite has optional add-on features, including Remote Help, Endpoint Privilege Management, Microsoft Tunnel for MAM, and more.
For more information, go to Intune Suite add-on features
Learn how you can benefit from modern endpoint management with Microsoft Intune.
Integrates with other Microsoft services and apps
Microsoft Intune integrates with other Microsoft products and services that focus on endpoint management, including:
Configuration Manager for on-premises endpoint management and Windows Server, including deploying software updates and managing data centers
You can use Intune and Configuration Manager together in a co-management scenario, use tenant attach, or use both. With these options, you get the benefits of the web-based admin center and can use other cloud-based features available in Intune.
For more specific information, go to:
- What is co-management
- Frequently asked questions about co-management
- How to enable tenant attach
Windows Autopilot for modern OS deployment and provisioning
With Windows Autopilot, you can provision new devices and send these devices directly to users from an OEM or device provider. For existing devices, you can reimage these devices to use Windows Autopilot and deploy the latest Windows version.
- Windows Autopilot overview
- Windows Autopilot deployment for existing devices
Endpoint analytics for visibility and reporting on end user experiences, including device performance and reliability
You can use Endpoint analytics to help identify policies or hardware issues that slow down devices. It also provides guidance that can help you proactively improve end user experiences and reduce help desk tickets.
- What is Endpoint analytics
- Enroll Intune devices into Endpoint analytics
Microsoft 365 for end user productivity Office apps, including Outlook, Teams, Sharepoint, OneDrive, and more
Using Intune, you can deploy Microsoft 365 apps to users and devices in your organization. You can also deploy these apps when users sign in for the first time.
- Add Microsoft 365 Apps to Windows 10/11 devices with Microsoft Intune
- Microsoft 365 docs: Manage devices with Intune
Microsoft Defender for Endpoint to help enterprises prevent, detect, investigate, and respond to threats
In Intune, you can create a service-to-service connection between Intune and Microsoft Defender for Endpoint. When they're connected, you can create policies that scan files, detect threats, and report threat levels to Microsoft Defender for Endpoint. You can also create compliance policies that set an allowable level of risk. When combined with conditional access, you can block access to organization resources for devices that are noncompliant.
- Enforce compliance for Microsoft Defender for Endpoint with Conditional Access in Intune
- Configure Microsoft Defender for Endpoint in Intune
Windows Autopatch for automatic patching of Windows, Microsoft 365 apps for enterprise, Microsoft Edge, and Microsoft Teams
Windows Autopatch is a cloud based service. It keeps software current, gives users the latest productivity tools, minimizes on-premises infrastructure, and helps free up your IT admins to focus on other projects. Windows Autopatch uses Microsoft Intune to manage patching for Intune-enrolled devices or devices using co-management (Intune + Configuration Manager).
- What is Windows Autopatch?
- Frequently Asked Questions about Windows Autopatch
Integrates with third party partner devices and apps
The Intune admin center makes it easy to connect to different partner services, including:
Managed Google Play : When you connect to your Managed Google Play account, admins can access your organization's private store for Android apps, and deploy these apps to your devices.
For more information, go to Add Managed Google Play apps to Android Enterprise devices with Intune .
Apple tokens and certificates : When they're added, your iOS/iPadOS and macOS devices can enroll in Intune and receive policies from Intune. Admins can access your volume purchased iOS/iPad and macOS app licenses, and deploy these apps to your devices.
- Get an Apple MDM push certificate
- Automatically enroll iOS/iPadOS devices by using Apple's Automated Device Enrollment
- Manage iOS and macOS apps purchased through Apple Business Manager with Microsoft Intune
TeamViewer : When you connect to your TeamViewer account, you can use TeamViewer to remotely assist devices.
For more information, go to Use TeamViewer to remotely administer Intune devices .
With these services, Intune:
- Gives admins simplified access to third party partner app services.
- Can manage hundreds of third party partner apps.
- Supports public retail store apps, line of business (LOB) apps, private apps not available in the public store, custom apps, and more.
For more platform-specific requirements to enroll third party partner devices in Intune, go to:
- Deployment guide: Enroll Android devices in Microsoft Intune
- Deployment guide: Enroll iOS and iPadOS devices in Microsoft Intune
- Deployment guide: Enroll Linux devices in Microsoft Intune
- Deployment guide: Enroll macOS devices in Microsoft Intune
Enroll in device management, application management, or both
Organization-owned devices are enrolled in Intune for mobile device management (MDM) . MDM is device centric, so device features are configured based on who needs them. For example, you can configure a device to allow access to Wi-Fi, but only if the signed-in user is an organization account.
In Intune, you create policies that configure features & settings and provide security & protection. The devices are fully managed by your organization, including the user identities that sign in, the apps that are installed, and the data that's accessed.
When devices enroll, you can deploy your policies during the enrollment process. When enrollment completes, the device is ready to use.
For personal devices in bring-your-own-device (BYOD) scenarios, you can use Intune for mobile application management (MAM) . MAM is user centric, so the app data is protected regardless of the device used to access this data. There's a focus on apps, including securely accessing apps and protecting data within the apps.
With MAM, you can:
- Publish mobile apps to users.
- Configure apps and automatically update apps.
- View data reports that focus on app inventory and app usage.
You can also use MDM and MAM together. If your devices are enrolled and there are apps that need extra security, then you can also use MAM app protection policies.
- What is device enrollment in Intune?
- App protection policies overview
- Create and assign app protection policies
Protect data on any device
With Intune, you can protect data on managed devices (enrolled in Intune) and protect data on unmanaged devices (not enrolled in Intune). Intune can isolate organization data from personal data. The idea is to protect your company information by controlling the way users access and share information.
For organization-owned devices, you want full control over the devices, especially security. When devices enroll, they receive your security rules and settings.
On devices enrolled in Intune, you can:
- Create and deploy policies that configure security settings, set password requirements, deploy certificates, and more.
- Use mobile threat defense services to scan devices, detect threats, and remediate threats.
- View data and reports that measure compliance with your security settings and rules.
- Use conditional access to only allow managed and compliant devices access to organization resources, apps, and data.
- Remove organization data if a device is lost or stolen.
For personal devices, users might not want their IT admins to have full control. To support a hybrid work environment, give users options. For example, users enroll their devices if they want full access to your organization's resources. Or, if these users only want access to Outlook or Microsoft Teams, then use app protection policies that require multi-factor authentication (MFA).
On devices using application management, you can:
- Use mobile threat defense services to protect app data by scanning devices, detecting threats, and assessing risk.
- Prevent organization data from being copied and pasted into personal apps.
- Use app protection policies on apps and on unmanaged devices enrolled in a third party or partner MDM.
- Use conditional access to restrict the apps that can access organization email and files.
- Remove organization data within apps.
- Protect data and devices with Microsoft Intune
- Mobile Threat Defense integration with Intune
Simplify access
Intune helps organizations support employees who can work from anywhere. There are features you can configure that allow users to connect to an organization, wherever they might be.
This section includes some common features that you can configure in Intune.
Use Windows Hello for Business instead of passwords
Windows Hello for Business helps protect against phishing attacks and other security threats. It also helps users sign in to their devices and apps more quickly and easily.
Windows Hello for Business replaces passwords with a PIN or biometric, such as fingerprint or facial recognition. This biometric information is stored locally on the devices and is never sent to external devices or servers.
- Windows Hello for Business Overview
- Manage Windows Hello for Business on devices when they enroll in Intune
Create a VPN connection for remote users
VPN policies give users secure remote access to your organization network.
Using common VPN connection partners, including Check Point, Cisco, Microsoft Tunnel, NetMotion, Pulse Secure, and more, you can create a VPN policy with your network settings. When the policy is ready, you deploy this policy to your users and devices that need to connect to your network remotely.
In the VPN policy, you can use certificates to authenticate the VPN connection. When you use certificates, your end users don't need to enter usernames and passwords.
- Create VPN profiles to connect to VPN servers in Intune
- Use certificates for authentication in Microsoft Intune
- Microsoft Tunnel for Microsoft Intune
- Microsoft Tunnel for MAM
Create a Wi-Fi connection for on-premises users
For users who need to connect to your organization network on-premises, you can create a Wi-Fi policy with your network settings. You can connect to a specific SSID, select an authentication method, use a proxy, and more. You can also configure the policy to automatically connect to Wi-Fi when the device is in range.
In the Wi-Fi policy, you can use certificates to authenticate the Wi-Fi connection. When you use certificates, your end users don't need to enter usernames and passwords.
When the policy is ready, you deploy this policy to your on-premises users and devices that need to connect to your on-premises network.
- Create Wi-Fi policy to connect to Wi-Fi networks in Intune
Enable single sign-on (SSO) to your apps and services
When you enable SSO, users can automatically sign in to apps and services using their Microsoft Entra organization account, including some mobile threat defense partner apps.
Specifically:
On Windows devices, SSO is automatically built in and used to sign in to apps and websites that use Microsoft Entra ID for authentication, including Microsoft 365 apps. You can also enable SSO on VPN and Wi-Fi policies.
On iOS/iPadOS and macOS devices, you can use the Microsoft Enterprise SSO plug-in to automatically sign in to apps and websites that use Microsoft Entra ID for authentication, including Microsoft 365 apps.
On Android devices, you can use the Microsoft Authentication Library (MSAL) to enable SSO to Android apps.
- How SSO to on-premises resources works on Microsoft Entra joined devices
- Use the Microsoft Enterprise SSO plug-in on iOS/iPadOS and macOS devices in Microsoft Intune
- Enable cross-app SSO on Android using MSAL
- Manage apps using Microsoft Intune
Was this page helpful?
Coming soon: Throughout 2024 we will be phasing out GitHub Issues as the feedback mechanism for content and replacing it with a new feedback system. For more information see: https://aka.ms/ContentUserFeedback .
Submit and view feedback for
Additional resources

Michal Machniak
MCT/MCSE/MCSA SysOps and DevOps working in IT over 15 years.
- Custom Social Profile Link
Intune (Endpoint Manager) - How to deploy Office templates and keep them up to date (recurring).
8 minute read

Why I write this article
Organization often use custom office templates that are available in Word/Excel/PowerPoint as custom. Those templates contain logs, footers of organization and custom fonts.
IT ops deploy custom office and templates to End User devices using Group Policy in Active Directory and file share to store those custom office templates . This task is common but have few limitations:
- Users need to be connected over VPN and have access to file share
- Custom templates don’t update after change on file share
- This solution requires Active Directory management
To allow move management to Intune and keep business process of delivering custom office templates to devices that are manage by Intune and don’t connect to Active Directory we develop this solution base on PowerShell scripts.
Intune witch PowerShell scripts also have some limitations like
- PowerShell scripts deploy by won’t run schedule time all time
- Intune agent don’t have any profile
To avoid these limitations, we split this solution to 2 parts:
- Registered solution on local computer that will in dedicated schedule call script.
- Call script each time when will be running will download fresh custom office templates to local drive.
On this article I will show how to do it with full cloud based solution, for this I will use Azure storage account and Intune with PowerShell .
Prerequisites
On this article we will use:
- Azure storage account
- Intune (Endpoint Manager)
- PowerShell scripts
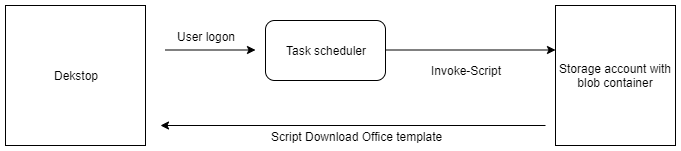
General flow and execution
Templates will be refreshed each time user log on to PC by scheduler task that will execute script form URL
Azure subscription creation
First we will need to create free Azure Subscription:
Link : Create Free Azure account Guide:
Azure storage account configuration
To storage office templete and script responsible for deploying templates in local machine, we will use azure storage account with public blob container . Storage account is one of cheaper solution to keep data use in this solution. Cost is based on amount of data counted in GB per month so for scripts and documents template it won’t be so match.
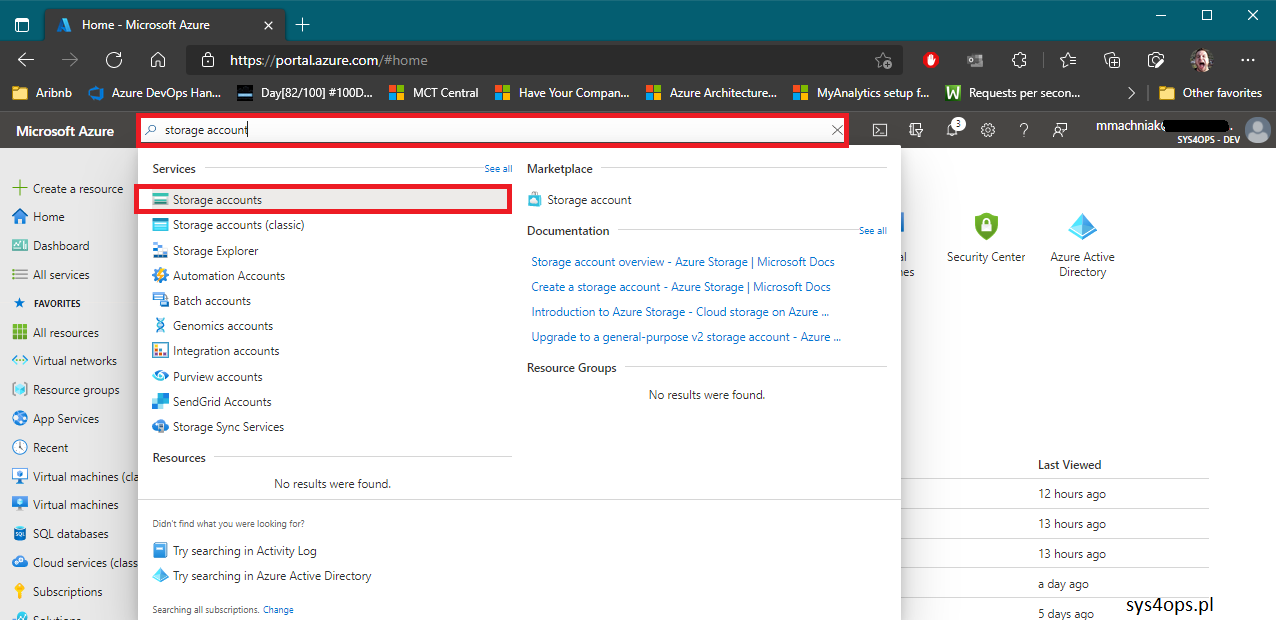
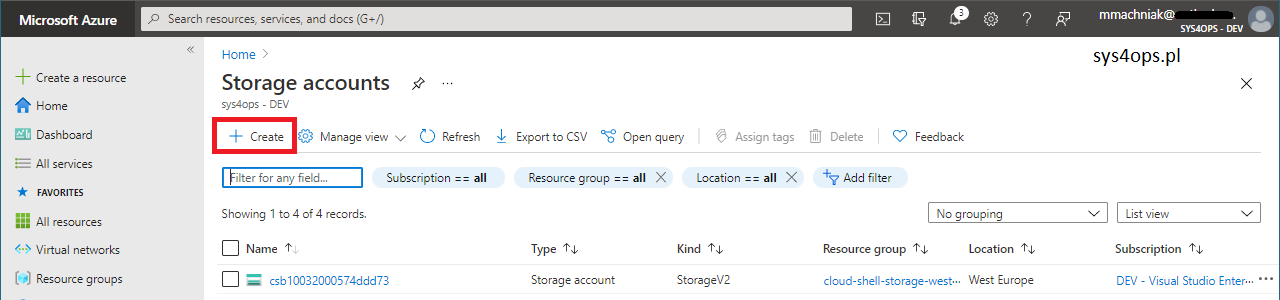
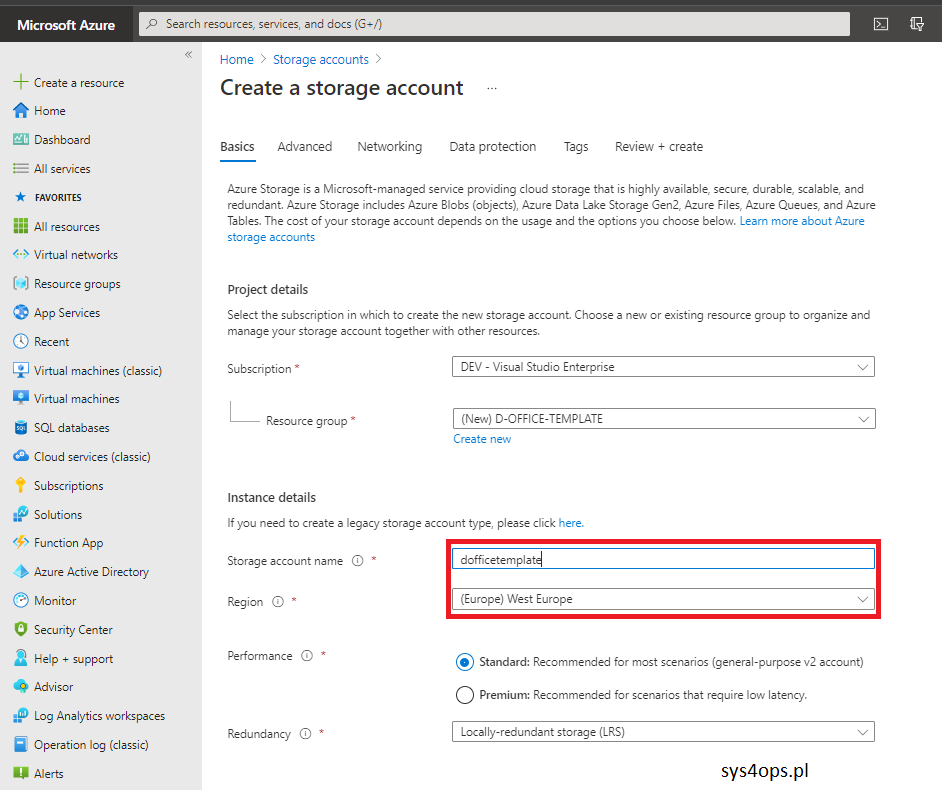
Create storage account in Azure
a) Logon to https://portal.azure.com b) On top search bar type storage account
c) On navigation bar click Create
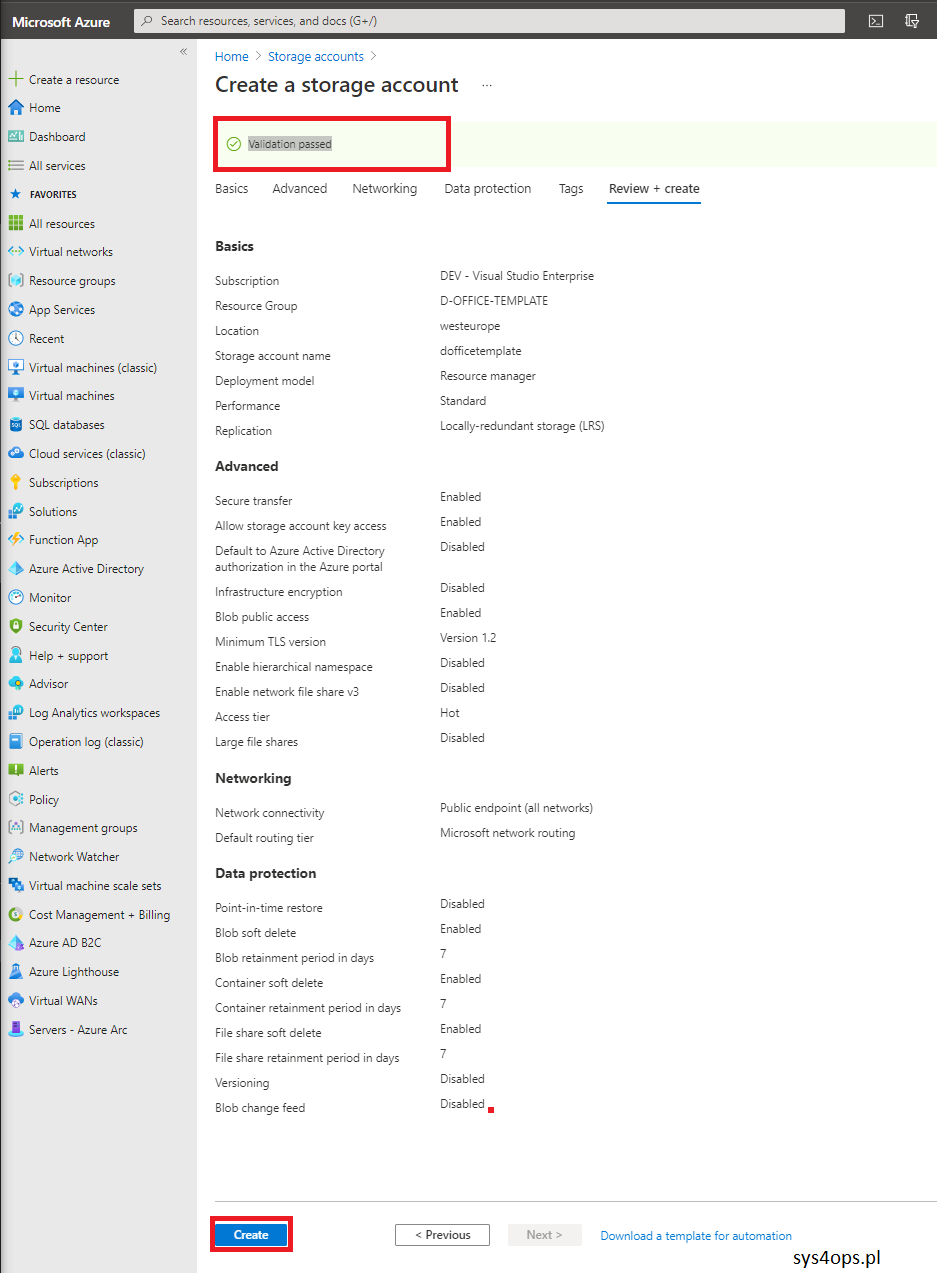
d) Enter data in Basic tab
e) On Advanced tab click Next f) On Networking tab click Next g) On Data protection tab click Next h) On Tags tab click Next i) On Review + Create tab click Create if Validation passed
Create public blob on storage account
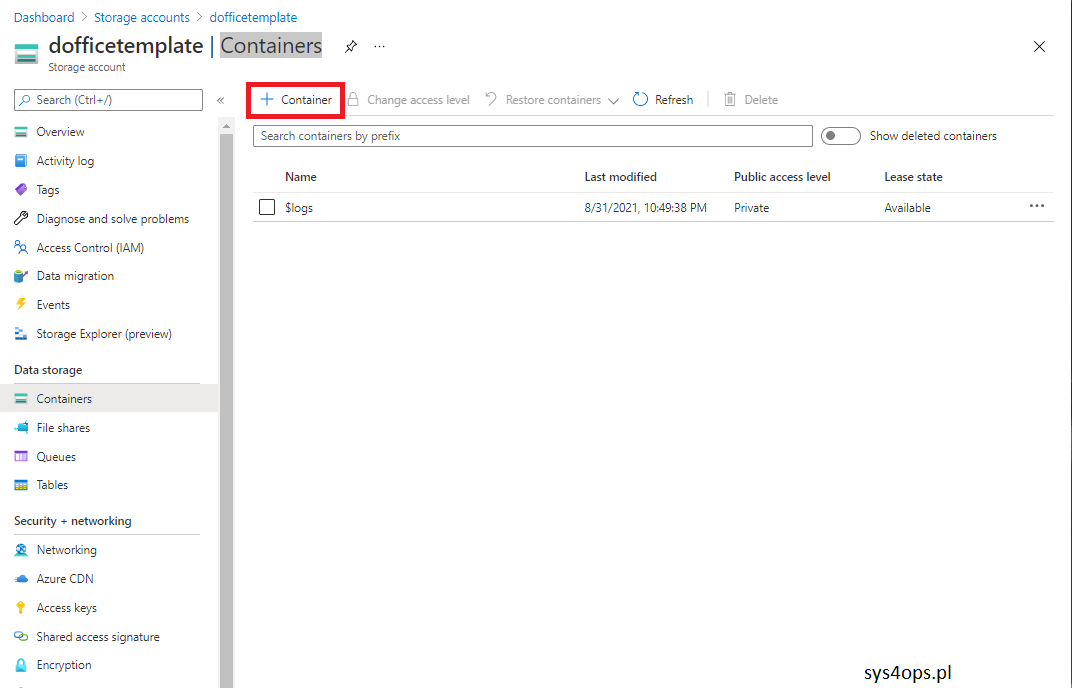
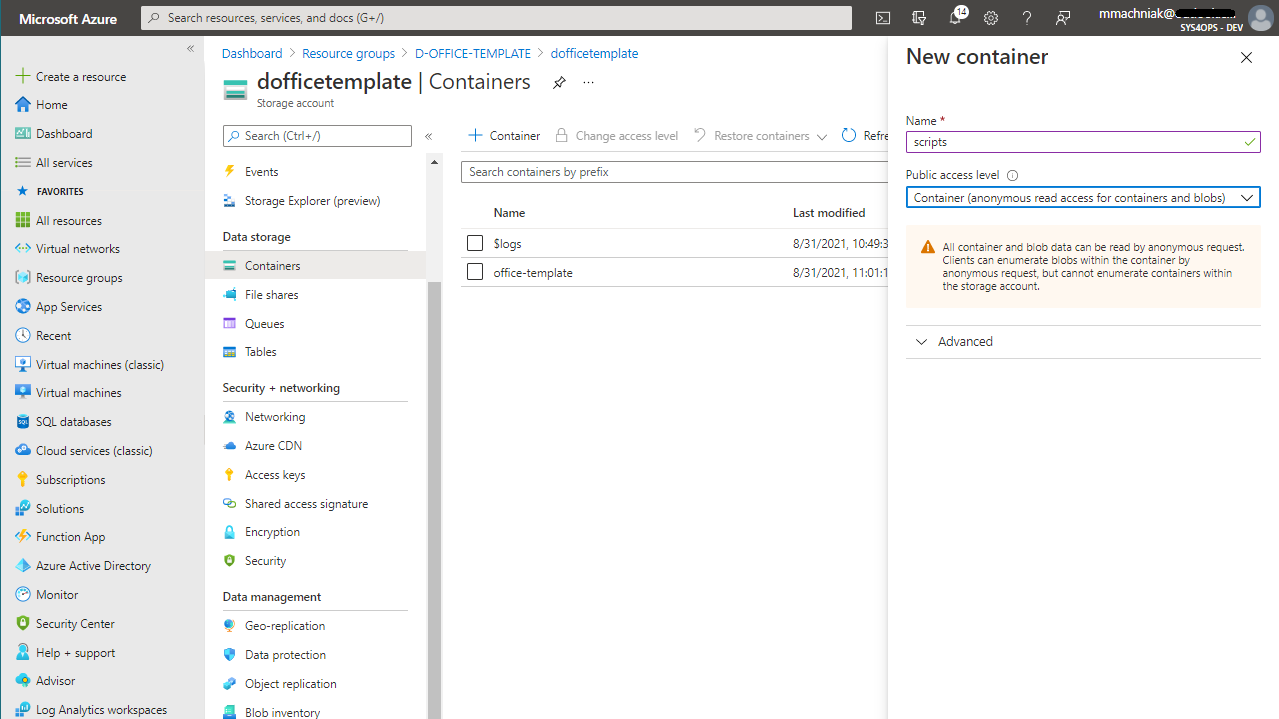
a) Logon to https://portal.azure.com b) On top search bar type storage account c) Click on storage account created previously d) On left navigation menu click on Containers and n navigation bar click Container
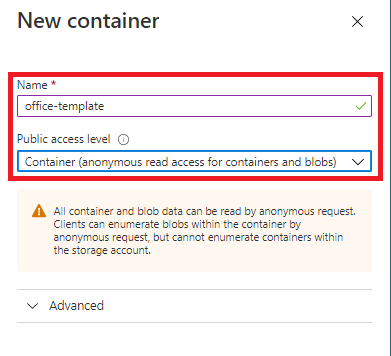
e) Enter date for new container and chage public access level then click Create
f) Upload office template files by clicking Upload on navigation menu
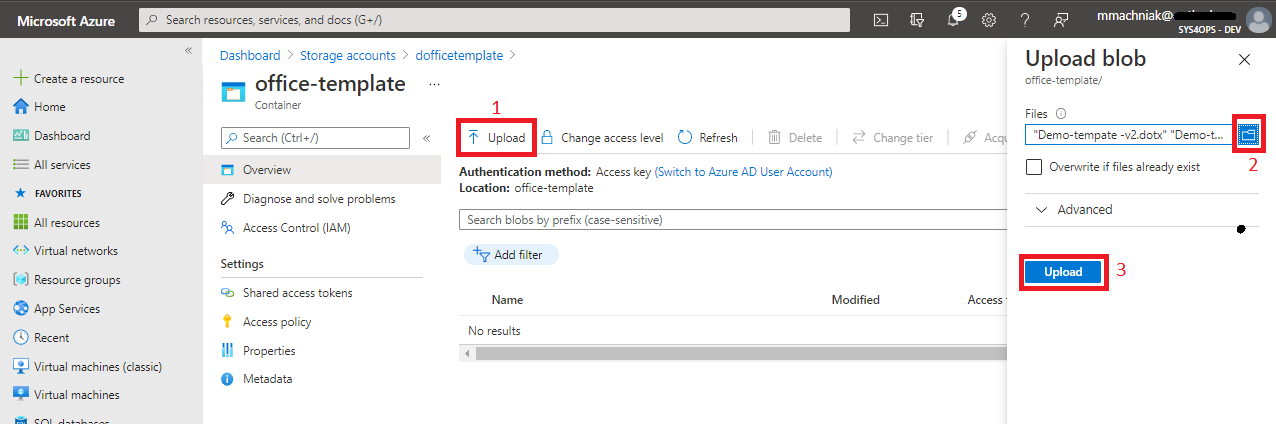
g) Click on created container with name scripts and upload script
PowerShell scripts data preparation for all actions
Powershell scripts used for this solution can be found on my repository in GitHub under this link: https://github.com/mimachniak/sysopslife-scripts/tree/master/Intune
Script responsible for downloading templates to local environment
First, we will prepare script that is responsible for downloading Office templates form Storage account to local drive and put those templates in dedicated folder that is also set by this script. So as starting point you need to prepare configuration parameters dedicated for your organization or use my.
a) Change parameter date dedicated for your environment, script can be downloaded form GitHub: Intune-DocumentTemplateStorageAccount.ps1
Parameters that need to be change for you environment
b) Storage account Name is available in Endpoints section in Azure on Blob
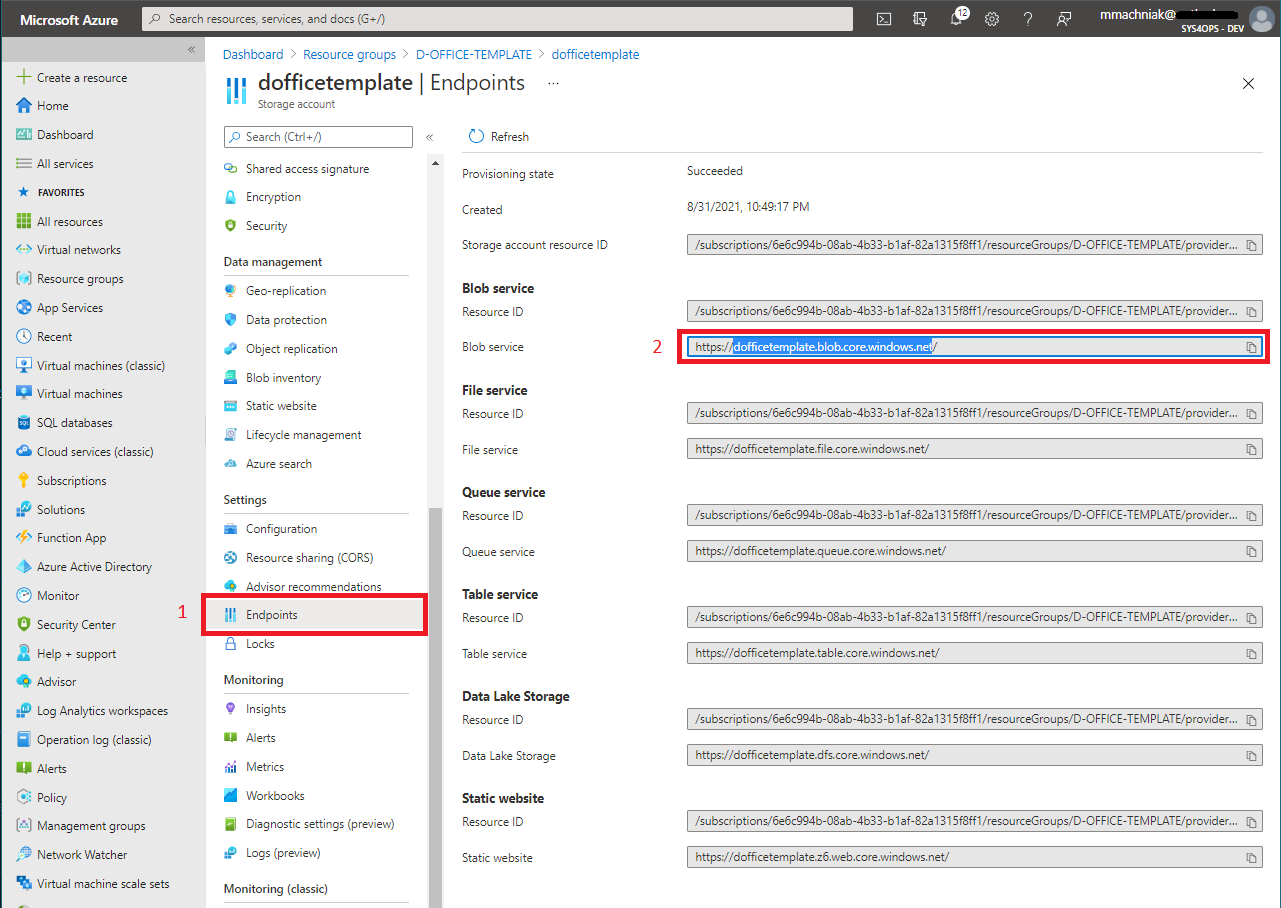
Full script body will look like this
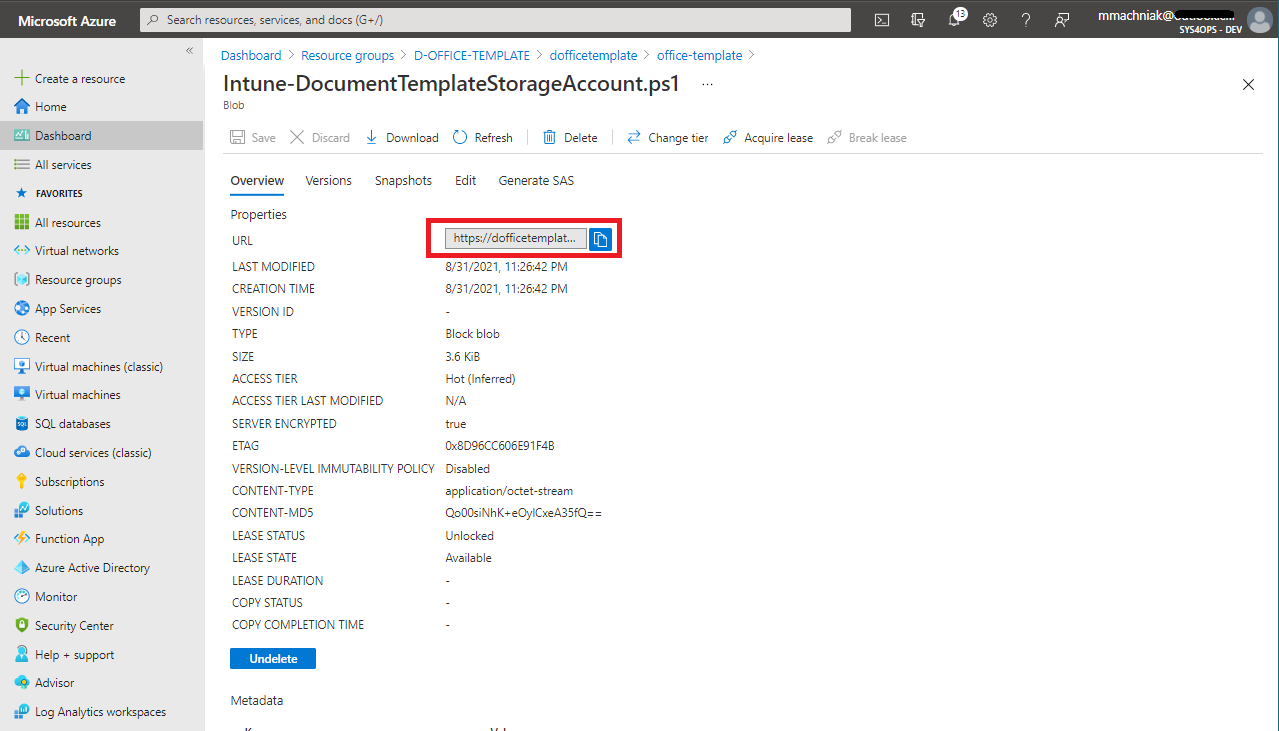
c) Upload script to Container on storage account, the same container name scripts
d) Click on uploade script with name Intune-DocumentTemplateStorageAccount.ps1 f) Copy URL and past it to second script that will be deploy by Intune
Script responsible registering by Intune task scheduler that will execute script each time user log in to desktop.
a) Change parameter data dedicated for your environment, script can be downloaded form my repository on GitHub: Windows10-taskScheduler-register-executescript-url.ps1
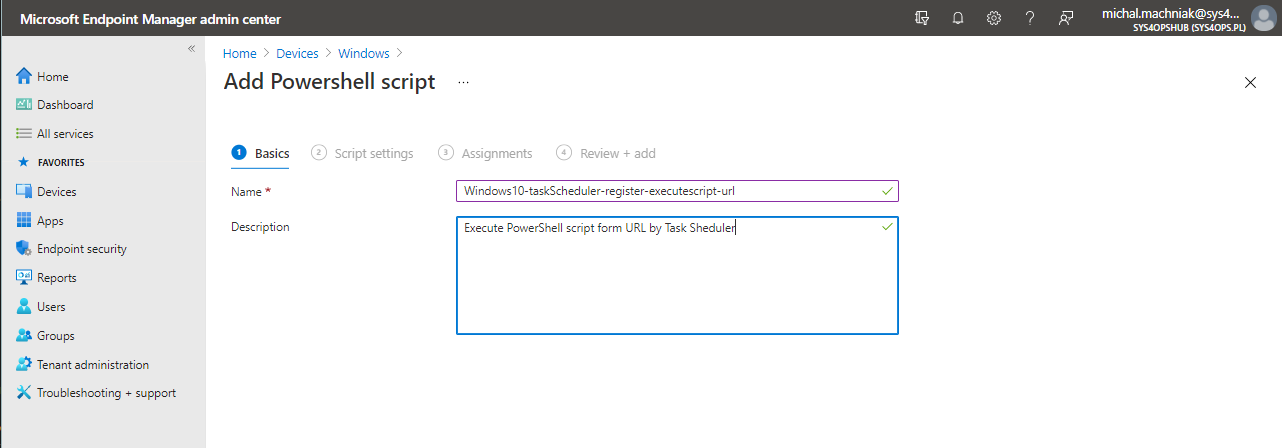
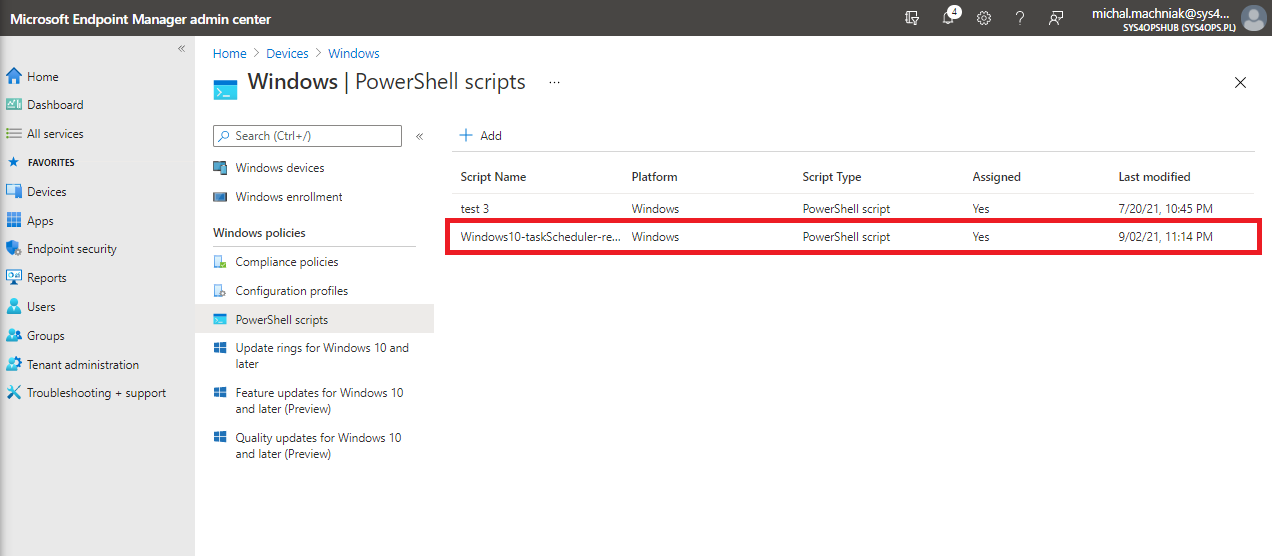
b) Logon to https://endpoint.microsoft.com https://endpoint.microsoft.com with minimum permission as Intune Administrator c) In Endpoint Manager Console navigate to section Devices –> Windows –> PowerShell scripts
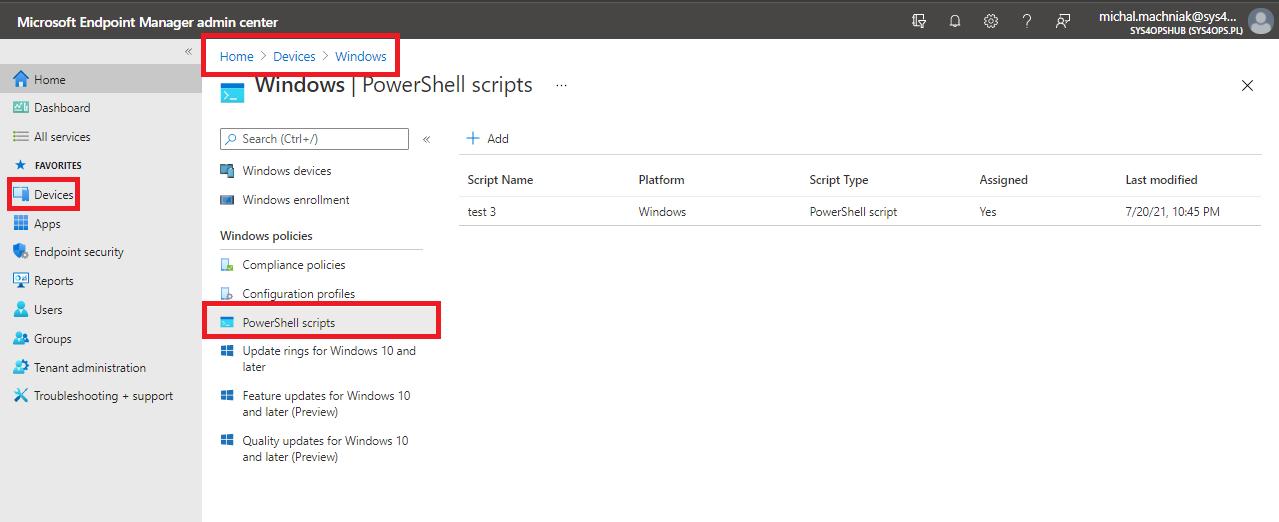
d) On navigation click Add f) Enter Name and Description
g) On Script Settings add script and select Run this script using the logged on credentials
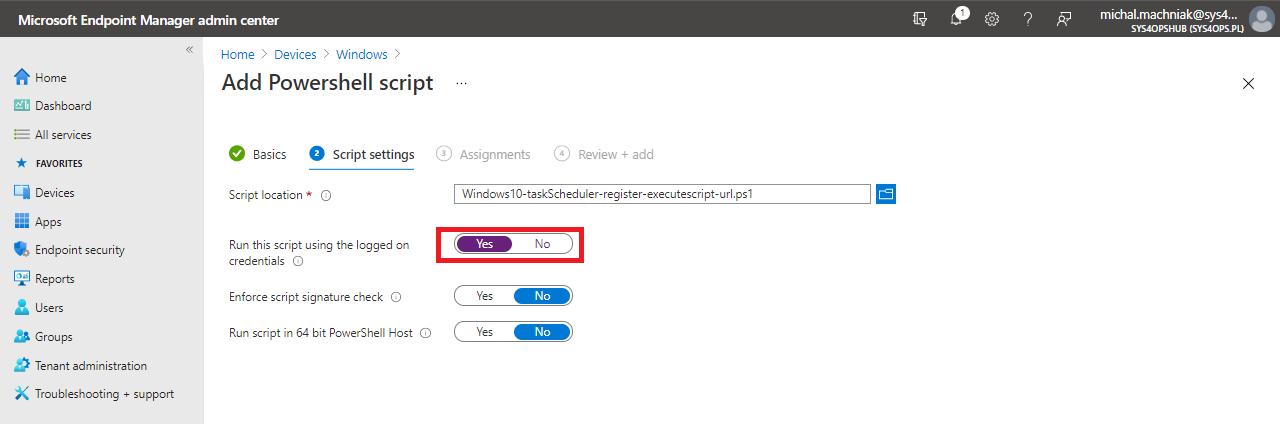
The script runs with the users’ credentials on the client computer. By default, the script runs in system context.
f) On Assignments and All Users or selected dedicated group of Users for which you like to implement this solution
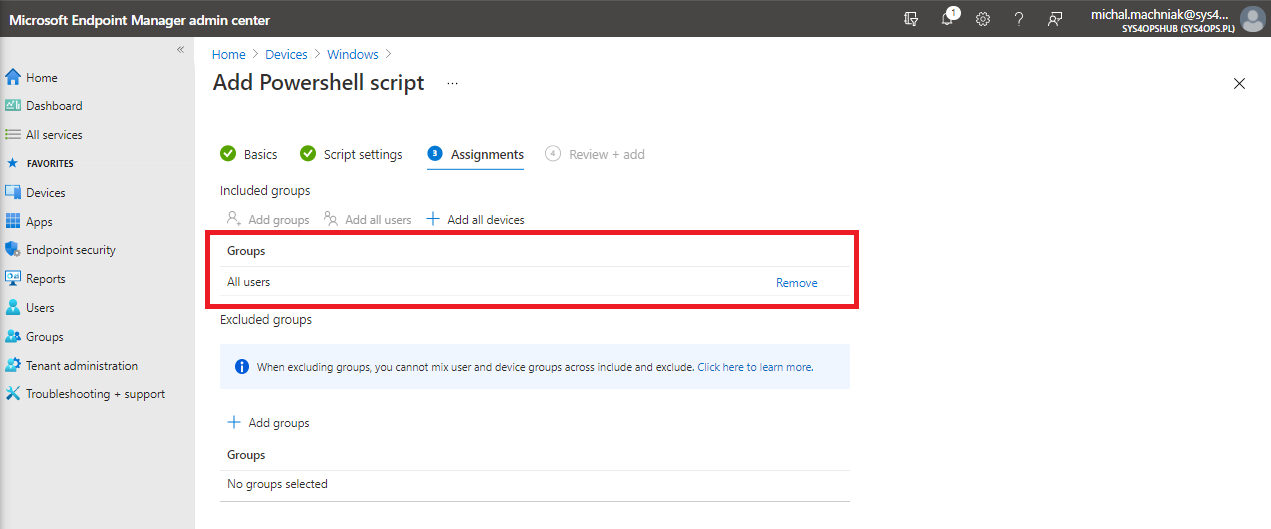
h) Click Next and Add
Windows 10 verification
Intune policy synchronization force.
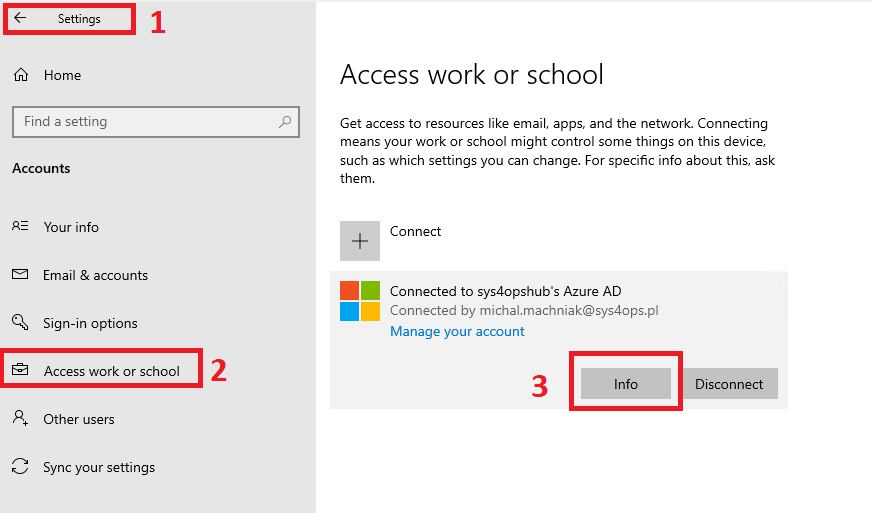
a) Log on to device b) Navigate to Settings –> Accounts –> Access work or school b) Click on connection and then on Info
c) Scroll down and click on Sync
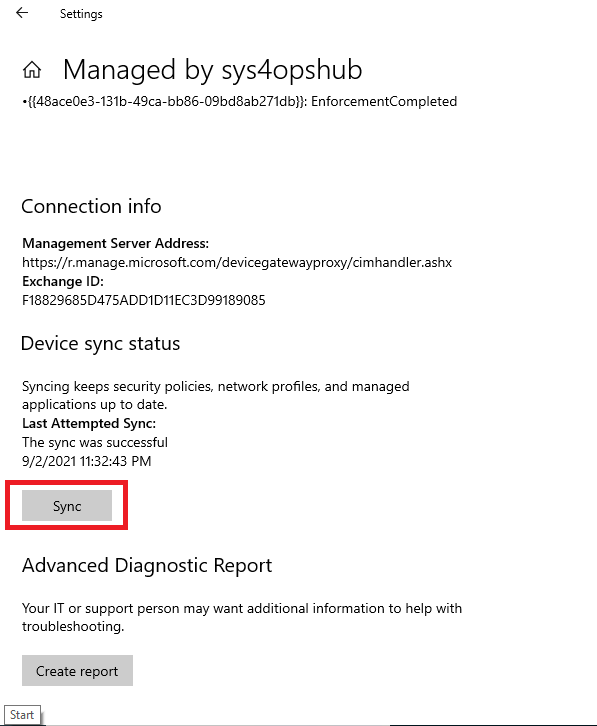
d) After sync completed (can take to 90 min) go to task scheduler and verify that new task was registered under Task Scheduler Library e) Verify that task was registered on Windows 10 in Task Scheduler Library
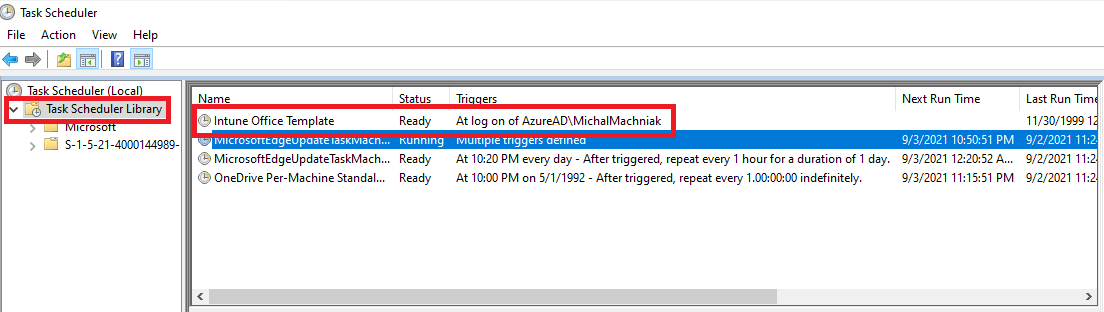
f) Run taks in *task scheduler and verify that templates was downloaded to local folder or re-logon user to trigger task scheduler
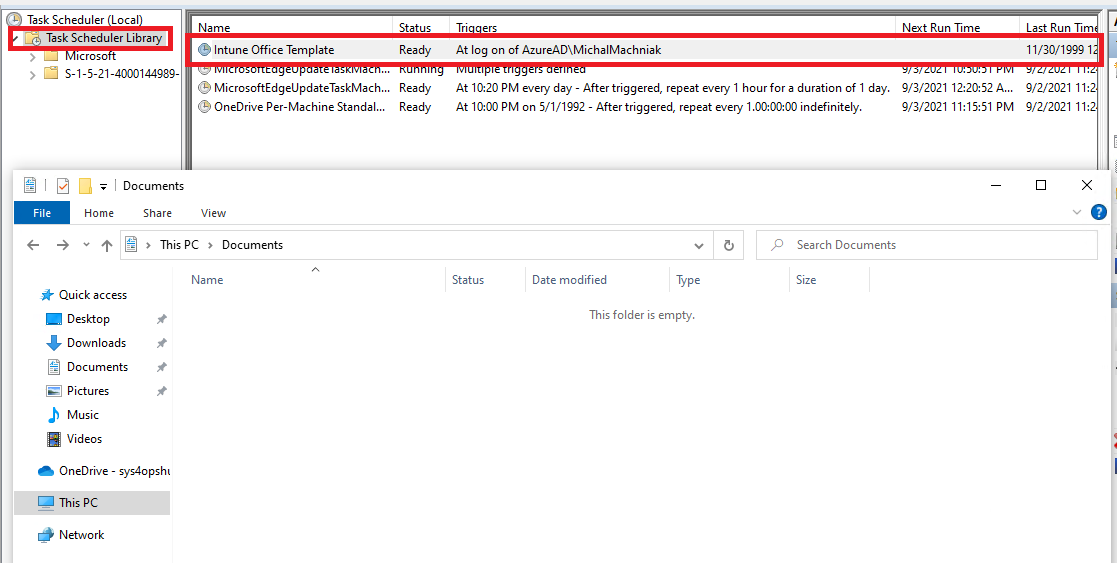
g) Verify that after task run templates files are downloaded to designated location on local hard drive
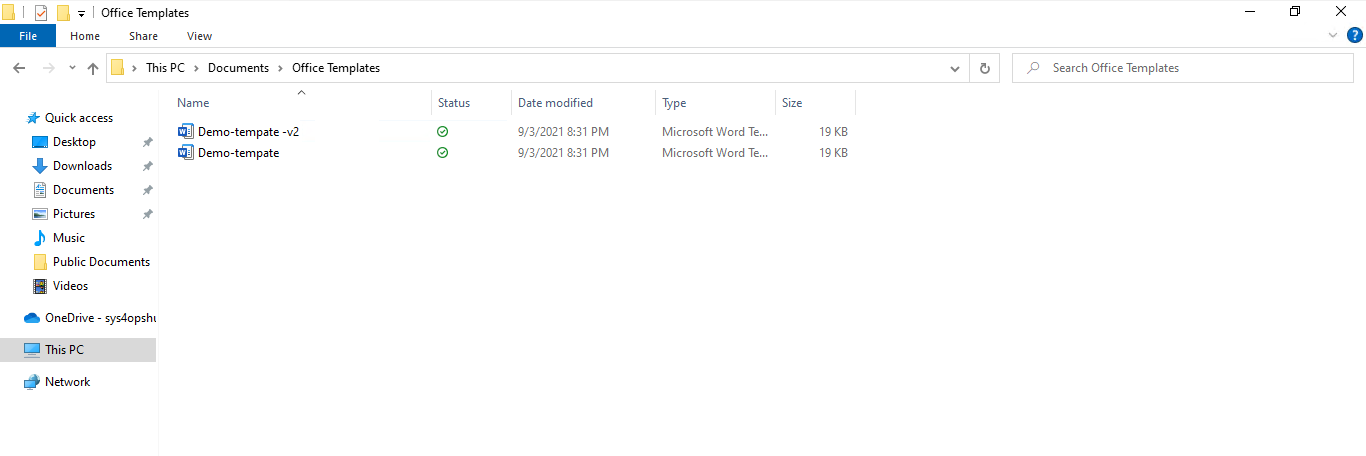
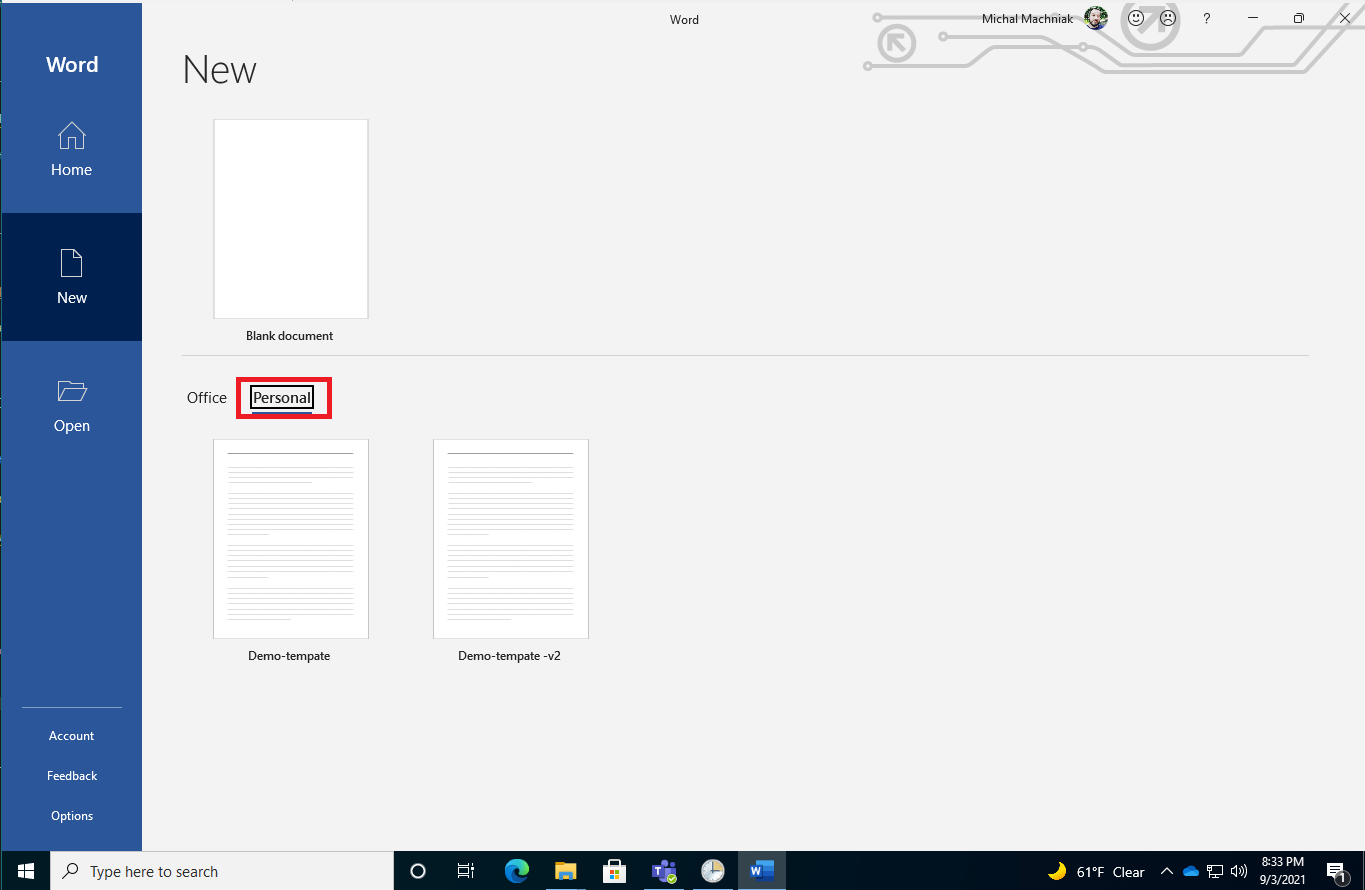
i) Verify that Microsft Word and Excel show document templates in section Personal
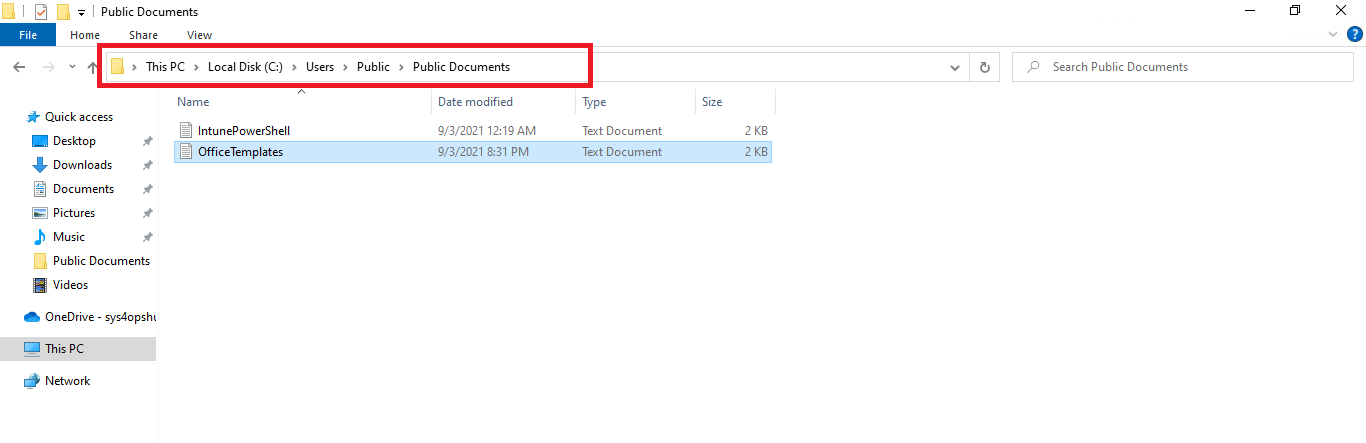
j) Log files will be created for each action and replace each run under path C:\Users\Public\Documents all logs are super pass on each run
- IntunePowerShell.log - Contains logs of Intune executing tasks that will runs script responsible for registering in Task Scheduler Library recurring task that responsible for downloading Office templates to local drive
- OfficeTemplates.log - Contains logs of script that is responsible for downloading templates to local drive, script is executed form URL
I hope this article will allow to eliminate in your organization another step that block you witch moving to cloud, if you like this post please share it or send feedback.
Leave a comment
You may also enjoy.

Microsoft 365 Global Private Access Setup and replace classic VPN.
3 minute read
Private Access is new solution that allow to access internal resources, it replace classic VPN with identity-centric Zero Trust Network Access (ZTNA).
Microsoft 365 Graph synchronization GAL to SharePoint Online List across multiple tenants.
11 minute read
Microsoft 365 Graph synchronization GAL to SharePoint Online List accross multiple tenants.
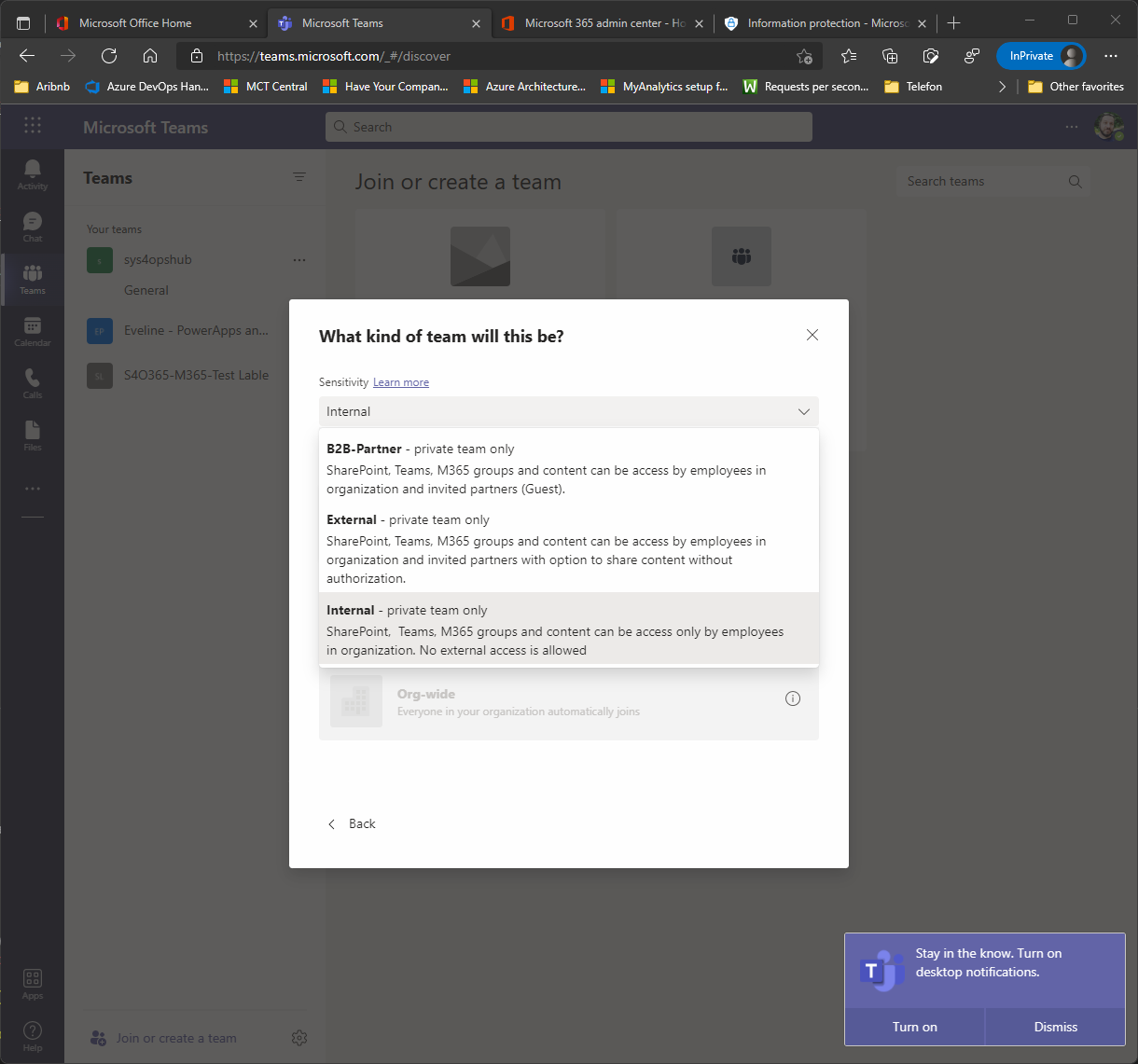
Microsoft 365 Groups – Sensitive labels assignment for data protection and external sharing.
SharePoint Online - Guest access to site or OneDrive will expire automatically after period of time.
SharePoint Online - New Guest expire policy that will remove access for guest account after period of time form SharePoint Site and OneDrive.

- Tips and guides
- Microsoft 365
The business case for endpoint management modernization according to Microsoft
- Steve Dispensa, Corporate Vice President, Enterprise Management and Windows Commercial
- Enterprise Mobility + Security
- Small business
- Forrester Research
- Gartner Magic Quadrant
- Zero Trust Security
Is your Chief Financial Officer (CFO) asking you to cut costs? This is a current theme with many of the Chief Technology Officers (CTOs) I speak with. After all, inflation in the United States is now at 8.5 percent, meaning higher input costs for businesses. 1 This includes staff—Skillsoft reported that the number of IT decision-makers facing a talent shortage has grown to 76 percent, 2 meaning wages are increasing for in-demand IT employees. 3 Furthermore, the cost of recruiting and retaining IT staff has increased. Any CTO who can help the CFO with Benjamin Franklin’s old phrase “a penny saved is a penny earned” will win plaudits in the C-suite. 4
Yet the “penny saved” dictum needs to be updated from the 18 th century to be helpful. It is important to not just think about reducing the price of software licenses by a few percent but to understand the total cost of ownership, including the value of employee time and hidden costs, such as ongoing productivity losses caused by security breaches. It’s also important to recognize that business cases may have changed in the past couple of years because of changes in staff costs or the cost of cyber breaches.
Given this context, this blog post proposes some new ways of thinking about the economics of unified endpoint management (UEM). We’ll start by recapping the main savings you’ll see in a business case for UEM, 5 before talking about recent industry trends and how they change how some customers are calculating the value of implementing UEM.
Recapping the business case for unified endpoint management
An independent Forrester analysis 5 described three of the main benefits of Microsoft’s unified endpoint management:
- The savings from reduced support tickets due to more automated endpoint security.
- The savings from centralizing endpoint management by attaching on-premises devices to the cloud.
- Reducing the risk of a security breach and the associated costs from data loss.
Reducing support needs
The first plank of the business case is how unified endpoint management reduces support needs. The logic is straightforward: fewer support tickets result in fewer hours spent by helpdesk staff. For a 2021 commissioned Total Impact™ study of Microsoft Endpoint Manager , 5 Forrester Consulting independently interviewed enterprise organizations to help benchmark the scale of the savings in reducing support needs. The savings can be thought of in terms of the support required at every stage of the user lifecycle. For example, Forrester estimates reductions in the time required to configure a new endpoint or to set up a new user on a laptop. These organizations told Forrester that the time taken to set up a new laptop can be cut by 25 percent for both users and IT admins in some cases, which is significant if it previously took a combined total of six hours to get a new employee up and running. 6 After that, there is the general reduction in support tickets by users who have less need to call the helpdesk (through proactive, automation of issues before the user is even aware, for example). Our customers tell us they have seen a 20 to 40 percent reduction in tickets after the modernization of their endpoints . 5 They also tell us there are further savings in helpdesk staff being able to resolve existing tickets faster by reducing the complexity of the tickets they are handling. All in all, the automation of workflows from unified endpoint management saves IT time, which can then be redeployed to more strategic projects.

Centralizing endpoint management and connecting on-premises devices to the cloud
The second part of the business case is the ability to centralize endpoint management and thus reduce fragmented costs. Allowing IT admins to manage devices from anywhere provides for greater staffing flexibility and economies of scale as IT admins can manage endpoints from one console, rather than separate panes of glass. It also ensures devices are configured and up to date with the latest security patches, whether the device is on a local network or not.
Some of the business case for this will be counted below, in reducing the risk of a security breach. Yet centralization also opens the ability to reconsider spending on overlapping technology and staff costs. For example, this might result in some legacy software savings, either through subscriptions, licenses, or maintenance costs. Additionally, the overhead costs of managing several vendors that support different device platforms or that provide services adjacent to endpoint management may be reduced by consolidating into a single solution. Equally, there might be on-premises hardware costs that can be re-examined. Lastly, customers tell us of staff time savings: onsite IT admins and network engineer hours can both be reduced significantly with this approach.
Reducing the risk of data breaches or non-compliance
Finally, unified endpoint management helps reduce the risk of data breaches. Forrester estimates the lost productivity of a security breach per affected employee at almost half a working day (about 3.5 hours) per year, 5 as they may need to update their device with the latest patch or recover work or data that is impacted by the breach. Reducing the risk of a data breach by 30 to 50 percent (as some of our customers have estimated, especially as part of a broader Zero Trust approach) therefore results in significant enterprise savings. On top of the lost employee productivity costs, there are direct out-of-pocket costs of a data breach, such as the extra work in remediating the breach and possible increases in insurance premiums.
Updating the 2022 endpoint management business case for today’s world of work
So why am I encouraging you to revisit the business case for moving to cloud-based endpoint management? In short, two major things have changed. First, rising IT staff costs mean the relative value of automated solutions is higher than before. Second, the shift to remote and hybrid work has increased the average cost and risk of a data breach for companies, making the cost of not acting higher. 7

First, statistics indicate an extremely tight labor market for IT talent. In January 2022, there were roughly 340,000 unfilled IT job openings posted by employers, 8 11 percent higher than the average from the past 12 months. 8 Gartner® reports that “IT executives see the talent shortage as the most significant adoption barrier to 64% of emerging technologies, compared with just 4% in 2020.” 8 Further, those already employed in IT are looking elsewhere. An October 2021 survey from TalentLMS and Workable found that 72 percent of respondents in the United States are thinking of quitting their jobs in the next year. 9
These dynamics have resulted in wage inflation. The Information and Cyber Security Salary Guide revealed the median salary for security engineers with one to two years of experience has risen 7 percent in the past year in the United Kingdom, while United Kingdom information security managers with over five years of experience can expect a 9 percent pay rise this year. Across help desk staff, network engineers, IT admins, and security engineers, the more that can be automated, the fewer hours needed (and consequently the less need to hire more IT staff to handle organizational requests).
Second, the cost of a data breach is higher the more an organization has moved to remote and hybrid work environments. According to the Cost of a Data Breach report by IBM and the Ponemon Institute, the cost of data breaches rose nearly 10 percent year over year in 2021. Moreover, the average total cost of a data breach was 28 percent higher when remote working was a factor in causing the breach (USD4.96 million per breach, on average) compared to breaches where remote working was not a factor (USD3.89 million per breach, on average). This discrepancy rises the more staff work remotely. The average cost of a breach at organizations with 81 to 100 percent of employees working remotely is USD5.54 million compared to USD3.65 million for organizations with fewer than 10 percent of employees working remotely.
Despite the big cost impact of a potential data breach, there are small things that you can do or act on immediately.
First, if you haven’t already, proactively engage with your company’s CFO on the topic of strategic value, not just costs and budgets. As I said at the start, the relationship between CTO and CFO is increasingly vital in ensuring an organization performs optimally.
Second, as part of that discussion, I’d encourage you to nominate someone on your team to revisit the business case for UEM in light of staff wage inflation and higher breach costs. To help you along, here is a description of Forrester’s business case for UEM , and Microsoft can help you customize and calculate the business case to your circumstances.
Further reading:
- Microsoft Endpoint Manager
- Microsoft Endpoint Manager Total Economic Impact study
- Zero Trust Total Economic Impact study
- Modernizing Endpoint Management Total Economic Impact study
1 Consumer Price Index Summary , Economic News Release, U.S. Bureau of Labor Statistics.
2 3 out of 4 IT teams are facing critical skill gaps , Brandon Vigliarolo, TechRepublic. November 11, 2021.
3 Employment Cost Index Summary , Economic News Release, U.S. Bureau of Labor Statistics.
4 A Penny Saved is a Penny Earned , American Numismatic Association. October 6, 2019.
5 The Total Economic Impact ™ of Microsoft Endpoint Manager , Forrester Consulting. April 2021.
6 The Total Economic Impact ™ of Zero Trust Solutions from Microsoft , Forrester Consulting, December 2021.
7 Cost of a Data Breach Report 2021 , IBM Security, Ponemon Institute. 2021.
8 Gartner Press Release, “ Gartner Survey Reveals Talent Shortages as Biggest Barrier to Emerging Technologies Adoption ” September 13, 2021
GARTNER is the registered trademark and service mark of Gartner Inc., and/or its affiliates in the U.S. and/or internationally and has been used herein with permission. All rights reserved.
9 IT Workers Will Be Hard to Find and Keep in 2022 , Nicole Lewis, SHRM. December 13, 2021.
Related Posts

3 new ways the Microsoft Intune Suite offers security, simplification, and savings

Microsoft named a Leader in 2023 Gartner® Magic Quadrant™ for Unified Communications as a Service for the fifth year in a row

Microsoft recognized as a Leader in 2023 Gartner® Magic Quadrant™ for Desktop as a Service

3 ways to improve productivity and reduce costs with Microsoft Teams Phone
Look, It's Another Blog
Tech and Gaming, New and Old
Microsoft Endpoint Manager: A LouMug Presentation
This past November, I got the opportunity to present at the Louisville Microsoft Users Group. The topic this time was Microsoft Endpoint Manager, where I discussed the components of Endpoint Manager and how we are using the platform at work. The interaction from the audience was fantastic, with several people asking great questions and giving comments. A recording of the talk has been uploaded to YouTube for anyone who wants to watch. The slide deck is also available below, with embedded links to several resources.
Have fun, Tony

View, manage, and install add-ins for Excel, PowerPoint, and Word
When you enable an add-in, it adds custom commands and new features to Microsoft 365 programs that help increase your productivity. Because add-ins can be used by attackers to do harm to your computer, you can use add-in security settings to help protect yourself.
Note: This article only applies to Microsoft 365 applications running on Windows.
View installed add-ins

You can directly install add-ins from this page or select More Add-ins to explore.
In the Office Add-ins dialog, select My Add-ins tab.
Select an add-in you want to view the details for and right-click to select Add-in details option.
Click a heading below for more information .
Add-in categories explained
Active Application Add-ins Add-ins registered and currently running on your Microsoft 365 program.
Inactive Application Add-ins These are present on your computer but not currently loaded. For example, XML schemas are active when the document that refers to them is open. Another example is the COM add-in: if a COM add-in is selected, the add-in is active. If the check box is cleared, the add-in is inactive.
Document Related Add-ins Template files referred to by open documents.
Disabled Application Add-ins These add-ins are automatically disabled because they are causing Microsoft 365 programs to crash.
Add-in The title of the add-in.
Publisher The software developer or organization responsible for creating the add-in.
Compatibility Look here for any compatibility issues.
Location This file path indicates where the add-in is installed on your computer.
Description This text explains the add-in function.
Note: Microsoft Outlook has one add-in option in the Trust Center: Apply macro security settings to installed add-ins . InfoPath has no security settings for add-ins.
Permanently disable or remove an add-in
To disable or remove an add-in follow these steps:
Select File > Get Add-ins . Alternatively, you can select Home > Add-ins .
In the Office Add-ins dialog, select My Add-ins tab.
Select an add-in you want to remove and right click to select Remove option.
View or change add-in settings
You can see and change add-in settings in the Trust Center, descriptions of which are in the following section. Add-in security settings may have been determined by your organization so not all options may be available to change.
Select File > Get Add-ins .
Select More Add-ins > Manage My Add-ins.
Select Trust Center > Trust Center Settings > Add-ins.
Check or uncheck the boxes you want.
Add-in settings explained
Require Application Add-ins to be signed by Trusted Publisher Check this box to have the Trust Center check that the add-in uses a publisher's trusted signature. If the publisher's signature hasn’t been trusted, the Microsoft 365 program doesn’t load the add-in, and the Trust Bar displays a notification that the add-in has been disabled.
Disable notification for unsigned add-ins (code will remain disabled) When you check the Require Application Extensions to be signed by Trusted Publisher box, this option is no longer grayed out. Add-ins signed by a trusted publisher are enabled, but unsigned add-ins are disabled.
Disable all Application Add-ins (may impair functionality) Check this box if you don't trust any add-ins. All add-ins are disabled without any notification, and the other add-in boxes are grayed out.
Note: This setting takes effect after you exit and restart your Microsoft 365 program.
While working with add-ins, you may need to learn more about digital signatures and certificates , which authenticate an add-in, and trusted publishers , the software developers who often create add-ins.
Manage and install add-ins
Use the following instruction to manage and install add-ins.
To install a new add-in:
You can directly install popular add-ins on the page or go to More Add-ins to explore.
Select the add-in and select Add . Or browse by selecting Store tab in the Office add-in dialog to find other add-ins to install and select Add for that add-in.
To manage your add-ins:
Select File > Get Add-ins and from the bottom, select More Add-ins. Or select Home > Add-ins > More add-ins.
In the Office dialog, select My Add-ins tab. If you are not able to see your add-ins, select Refresh to reload your add-ins.
Select Manage My Add-in to manage and select Upload to browse and add an add-in from your device.
How to cancel a purchased add-in
If you've subscribed to an add-in through the Microsoft 365 Store that you don't want to continue, you can cancel that subscription.
Open the Microsoft 365 application and go to the Home tab of the ribbon.
Select Add-ins and then select More Add-ins > My Add-ins tab to view your existing add-ins.
Select the app you want to cancel and select Manage My Add-ins .
Under the Payment and Billing section choose Cancel Subscription .
Select OK and then Continue .
Once that's complete you should see a message that says "You have cancelled your app subscription" in the comments field of your apps list.
Why is my add-in crashing?
Some add-ins might not be compatible with your organization's IT department policies. If that is the case with add-ins recently installed on your Microsoft 365 program, Data Execution Prevention (DEP) will disable the add-in and the program might crash.
Learn more about DEP
Get a Microsoft 365 Add-in for Outlook
Get a Microsoft 365 Add-in for Project
Taking linked notes
If you're looking for Help on linking notes in OneNote to a Word or PowerPoint document, see Take linked notes .
Excel Windows Add-ins
If you're looking for Help on specific Excel Add-ins, such as Solver or Inquire, see Help for Excel for Windows add-ins .
If you're looking for additional help with Excel add-ins using the COM Add-ins dialog box, see Add or remove add-ins in Excel .
Get a Microsoft 365 Add-in for Excel

Need more help?
Want more options.
Explore subscription benefits, browse training courses, learn how to secure your device, and more.

Microsoft 365 subscription benefits

Microsoft 365 training

Microsoft security

Accessibility center
Communities help you ask and answer questions, give feedback, and hear from experts with rich knowledge.

Ask the Microsoft Community

Microsoft Tech Community

Windows Insiders
Microsoft 365 Insiders
Find solutions to common problems or get help from a support agent.

Online support
Was this information helpful?
Thank you for your feedback.

COMMENTS
9 Units. Microsoft Intune is your strategic infrastructure for managing and protecting your organization's devices, apps, and data. In addition, Microsoft Intune helps to ensure your end users have the best experience for productivity. This module helps explain endpoints that you need to protect, as well as the products and services that ...
Microsoft Intune Tenant Status page - A centralized hub where you can view current information and communications about the Intune service and your tenant status. Navigate to the Microsoft Endpoint Manager admin center. . Select Tenant administration > Tenant status > Service Health > Message center.
Advanced endpoint analytics* Cloud certificate management (PKI)* Endpoint Privilege Management 3rd-party app patching and packaging* Remote Help Microsoft Intune Bring together mission-critical management and security tools into a single, cloud-powered solution. The solution Simplify endpoint management Reduce TCO Protect hybrid workforce
Microsoft Endpoint Manager This learning path will help you understand how to manage and protect your organization's data, devices, and apps. The first module explains the products and services that encompass Microsoft Intune, as well as the value that each provides. You'll learn about the Intune environment and the supported platforms, such ...
Microsoft Intune is a family of products and services. The Intune family includes: Microsoft Intune service. Configuration Manager and co-management. Endpoint Analytics. Windows Autopilot. Intune admin center. These products and services offer a cloud-based unified endpoint management solution. It simplifies management across multiple operating ...
Benefits of the Workshop: By leveraging this Microsoft workshop, you will: • Learn how to improve your management capabilities with Microsoft Endpoint Manager. • Discover and protect your endpoints by enforcing policies and deploying security tools. • Secure your identities with multi-factor authentication and conditional access from any ...
Subject Matter Experts: Mayunk Jain , Joe Lurie. Leverage your existing investments in Configuration Manager to enable cloud value. Topics covered in this session: Co-managing devices with Microsoft Intune and Configuration Manager, Tenant Attach, Endpoint Analytics, Best Practices. 0 Likes.
Endpoint Manager (Intune) is Microsoft's cloud-based Enterprise Mobility Management (EMM) service that helps enable your workforce to be productive while keeping your corporate data protected ...
These convincing presentation slides are useful for Microsoft experts, endpoint administrators, and cloud experts to explain the features of an integrated management solution, such as cloud-powered intelligence, streamlined updates, and more. You can also depict how Microsoft Endpoint Manager works.
Support remote and hybrid workers with cloud native endpoints. Cloud-native endpoints are devices that can be deployed from anywhere. They receive their applications and configurations dynamically from the cloud, and can easily be reset or restored. Manage devices with Intune and Microsoft 365. A core component of enterprise-level security ...
To help with these challenges and tasks, use Microsoft Intune. Microsoft Intune is a cloud-based endpoint management solution. It manages user access to organizational resources and simplifies app and device management across your many devices, including mobile devices, desktop computers, and virtual endpoints.
Download our Microsoft Endpoint Manager PPT template to organize your information in a clean and clear way, leaving your viewers fascinated. The deck offers fuss-free editing. ... Give a meaningful insight into your ideas and information and impress your viewers; download this PowerPoint template now and create an outstanding presentation!
b) Logon to https://endpoint.microsoft.com https://endpoint.microsoft.com with minimum permission as Intune Administrator c) In Endpoint Manager Console navigate to section Devices -> Windows -> PowerShell scripts. d) On navigation click Add f) Enter Name and Description. g) On Script Settings add script and select Run this script using the logged on credentials
Microsoft Intune Microsoft Endpoint Manager Tenant attach Domain joined PCs (onDomain joined PCs-premises managed) Windows 10/11 CM + MDM Co-management workloads Windows and Mobile devices (cloud native managed) Cloud-only management ... PowerPoint Presentation Author: Mert Aksoy
Microsoft Endpoint Manager (Intune) is a 100% cloud-based mobile device management (MDM) and mobile ... PowerPoint Presentation Watch the recording of this webinar. 11:30 AM - 30 minutes . Learn how Microsoft Endpoint Manager helps deliver the modern workplace and modern management to keep your data secure, in the cloud and on-premises ...
The first plank of the business case is how unified endpoint management reduces support needs. The logic is straightforward: fewer support tickets result in fewer hours spent by helpdesk staff. For a 2021 commissioned Total Impact™ study of Microsoft Endpoint Manager, 5 Forrester Consulting independently interviewed enterprise organizations ...
Microsoft Endpoint Manager: LouMug 2021-11. This past November, I got the opportunity to present at the Louisville Microsoft Users Group. The topic this time was Microsoft Endpoint Manager, where I discussed the components of Endpoint Manager and how we are using the platform at work. The interaction from the audience was fantastic, with ...
Presentation of recommendation s and next steps We customize the workshop according to the needs of your organization: Establishment of the commitment: Microsoft Endpoint Manager Basic security Device configuration and management. Title: Presentación de PowerPoint Author: Luis Martínez
Here are the slides for the 4 sessions on Windows management. Thanks again! WinH3-Leveraging cloud updates to secure your devices with MEM.pdf. 1770 KB. WinH2-Policy Management on a Cloudy Day.pdf. 2208 KB. WinH4-Troubleshooting a Windows MDM device.pdf. 2223 KB. WinH1-Cloud Attach Your Organization.pdf.
Step 3: Operationalize and go to market. Take the final steps to transition your Cloud Endpoints practice from concept to reality. Partner with Microsoft. Engage with customers. Grow your business with Modern Work for Partners. Enable your customers in the cloud with one source for all the training, support, and tools you need.
Note: This article only applies to add-ins in Excel, PowerPoint, and Word.For guidance on how to view, install, and manage add-ins in Outlook, see Use add-ins in Outlook.