Research and Application of Digital Signature Technology
- Conference paper
- First Online: 11 November 2020
- Cite this conference paper

- Yanli Wang 12 , 13 ,
- Ying Zheng 12 &
- Fengyin Li 12
Part of the book series: Lecture Notes in Computer Science ((LNSC,volume 12486))
Included in the following conference series:
- International Conference on Machine Learning for Cyber Security
1155 Accesses
1 Citations
With the development of science and technology, the spread of images on the Internet is getting faster and faster, which also reduces the cost of infringement and brings immeasurable losses to image creators. In order to solve the problem of digital image infringement, this paper uses encryption algorithm and signature algorithm to design a verifiable message delivery scheme based on timestamp, and applies it to the copyright protection of digital image, designs and implements a copyright protection system based on digital signature and timestamp. Our system provides a new reference solution for the copyright registration protection of digital images, realizes the protection of digital image copyright through a small amount of encryption and decryption operations and a small amount of information transmission. After analysis, our copyright protection system has high computing efficiency and security, the calculation efficiency and advantages are more prominent when transmitting large data information, and it has good application prospects.
This is a preview of subscription content, log in via an institution to check access.

Access this chapter
- Available as PDF
- Read on any device
- Instant download
- Own it forever
- Available as EPUB and PDF
- Compact, lightweight edition
- Dispatched in 3 to 5 business days
- Free shipping worldwide - see info
Tax calculation will be finalised at checkout
Purchases are for personal use only
Institutional subscriptions
Making Timestamps a New Tool for Copyright Protection (2016)
Google Scholar
Baohu Duan, J.W.: New discussion on digital signature technology. Comput. Eng. Sci. (2009)
Barrett, P.: Implementing the Rivest Shamir and Adleman public key encryption algorithm on a standard digital signal processor. In: Odlyzko, A.M. (ed.) CRYPTO 1986. LNCS, vol. 263, pp. 311–323. Springer, Heidelberg (1987). https://doi.org/10.1007/3-540-47721-7_24
Chapter Google Scholar
Gao, L.: Research on digital signature technology based on public key algorithm. Master’s thesis, Southwest University of Science and Technology (2018)
Hu, J.: Research and implementation of RSA encryption algorithm. Ph.D. thesis, Anhui University of Technology (2011)
Huang, S.: Application of RSA digital signature algorithm in software encryption. Appl. Netw. Secur. Technol. 04 , 84–86 (2018)
Jiang, C.: Asymmetric encryption algorithm. Neijiang Sci. Technol. 8–148 (2012)
Lu, K.: Computer Cryptography. Tsinghua University Press, Beijing (2003)
Sun, W.: Improvement and implementation of public key RSA encryption algorithm. Ph.D. thesis, Anhui University (2014)
Wang, X.: Design of two digital signature schemes. Ph.D. thesis, Guizhou Normal University (2017)
Chen, Y., Peiqiang Cong, Z.C.: An improved scheme of elliptic curve digital signature. Res. Inf. Secur. 005 (003), 217–222 (2019)
Zhang, R.: Research and application of digital signature. Ph.D. thesis, Shaanxi Normal University (2015)
Zhang, S.: Research on a trusted timestamp service system based on identity authentication. Master’s thesis, Graduate School of Chinese Academy of Sciences (National Time Service Center) (2016)
Zhang, X.: Principle and Technology of Digital Signature. Mechanical Industry Press, Beijing (2004)
Zhang, X.: Legal protection of network copyright. Ph.D. thesis, Shandong University (2012)
Zhu, L.: High speed implementation of hash function encryption algorithm. Ph.D. thesis, Shanghai Jiaotong University (2007)
Download references
Author information
Authors and affiliations.
School of Information Science and Engineering, Qufu Normal University, Rizhao, 276826, China
Yanli Wang, Ying Zheng & Fengyin Li
School of Computer Science, Nankai University, Tianjin, 300071, China
You can also search for this author in PubMed Google Scholar
Corresponding author
Correspondence to Fengyin Li .
Editor information
Editors and affiliations.
Xidian University, Xi'an, China
Xiaofeng Chen
Guangzhou University, Guangzhou, China
Hongyang Yan
Michigan State University, East Lansing, MI, USA
Division of Computer, Electrical and Mathematical Sciences and Engineering, King Abdullah University of Science, Thuwal, Saudi Arabia
Xiangliang Zhang
Rights and permissions
Reprints and permissions
Copyright information
© 2020 Springer Nature Switzerland AG
About this paper
Cite this paper.
Wang, Y., Zheng, Y., Li, F. (2020). Research and Application of Digital Signature Technology. In: Chen, X., Yan, H., Yan, Q., Zhang, X. (eds) Machine Learning for Cyber Security. ML4CS 2020. Lecture Notes in Computer Science(), vol 12486. Springer, Cham. https://doi.org/10.1007/978-3-030-62223-7_47
Download citation
DOI : https://doi.org/10.1007/978-3-030-62223-7_47
Published : 11 November 2020
Publisher Name : Springer, Cham
Print ISBN : 978-3-030-62222-0
Online ISBN : 978-3-030-62223-7
eBook Packages : Computer Science Computer Science (R0)
Share this paper
Anyone you share the following link with will be able to read this content:
Sorry, a shareable link is not currently available for this article.
Provided by the Springer Nature SharedIt content-sharing initiative
- Publish with us
Policies and ethics
- Find a journal
- Track your research
- < Previous
Home > SCRIPPS > SCRIPPS_STUDENT > SCRIPPS_THESES > 1816
Scripps Senior Theses
Cryptography and digital signatures.
Maya Nichols , Scripps College Follow
Graduation Year
Document type.
Campus Only Senior Thesis
Degree Name
Bachelor of Arts
Mathematics
Christopher Towse
Douglas Goodwin
Terms of Use & License Information
Terms of Use for work posted in Scholarship@Claremont .
Rights Information
© 2022 Maya Nichols
What is security and what makes a cryptosystem secure? This thesis explores these questions by looking at the components of a couple public- key cryptosystems and digital signature schemes, attacks against them, and ways of improving security.

Recommended Citation
Nichols, Maya, "Cryptography and Digital Signatures" (2022). Scripps Senior Theses . 1816. https://scholarship.claremont.edu/scripps_theses/1816
This thesis is restricted to the Claremont Colleges current faculty, students, and staff.
Since May 26, 2022
Advanced Search
- Notify me via email or RSS
- Colleges, Universities, and Library
- Schools, Programs, and Departments
- Disciplines
Author Corner
- Faculty Submission
- Student Submission
- Policies and Guidelines
Useful Links
- Claremont Colleges Library
- Claremont Colleges Digital Library
Home | About | FAQ | My Account | Accessibility Statement
Privacy Copyright
- Uppsala University Library
- Subject Guides
Thesis Production
Digital signatures at uppsala university.
- About Thesis Production
- Booking a timeplan
- Accessibility
- Guide Order form Comprehensive summary
- New visual identity - Comprehensive summary
- Electronic publishing
- Reference management
- Technical issues
- Digital defence
- Licentiate theses
- Information session on thesis production
- Digitise your old thesis
A digital (electronic) signature is – like a regular signature on a piece of paper – a method for identification (of the person who wrote the document) or authenticity (so that the recipient of a signed document can be sure of who signed the document). Uppsala University offers two ways of signing documents digitally:
- Using the online service eduSign .
- Using a personal certificate and a PDF-reader.
At Thesis Production, you can sign these documents digitally:
- Approval of digital proof
Read more about Digital Signatures at Medarbetarportalen .
- << Previous: Digital defence
- Next: Licentiate theses >>
- Last Updated: May 6, 2024 8:38 AM
- URL: https://libguides-en.ub.uu.se/thesis
Digital Signature
Ieee account.
- Change Username/Password
- Update Address
Purchase Details
- Payment Options
- Order History
- View Purchased Documents
Profile Information
- Communications Preferences
- Profession and Education
- Technical Interests
- US & Canada: +1 800 678 4333
- Worldwide: +1 732 981 0060
- Contact & Support
- About IEEE Xplore
- Accessibility
- Terms of Use
- Nondiscrimination Policy
- Privacy & Opting Out of Cookies
A not-for-profit organization, IEEE is the world's largest technical professional organization dedicated to advancing technology for the benefit of humanity. © Copyright 2024 IEEE - All rights reserved. Use of this web site signifies your agreement to the terms and conditions.
Digital Signatures in The Business World Essay
In the business world, a signature is one of the most vital requirements when it comes to sealing of agreements. For instance, when two parties get into a contract, both parties must sign the contract as an indication of their commitment to the terms and conditions of the contract. In the event that one of them breaches the contract, these signatures may serve as evidence, in a court of law, that the parties were in an agreement.
Every handwritten signature is unique in terms of velocity, inclination angle and timing. This signature can be analyzed forensically against a sample signature to prove the identity of the signatory. A signature can be forged but it can never be duplicated: no two people can sign identically (Wright, 2007).
Unfortunately, this is only possible with pen and paper technology. With advancement in information technology, paper work has become almost obsolete. Transactions are carried out electronically hastening the whole process. However, this new development comes with its challenges; one of these challenges is how to attach a signature that is legally binding. In this paper, the legal issues of digital signatures will be discussed.
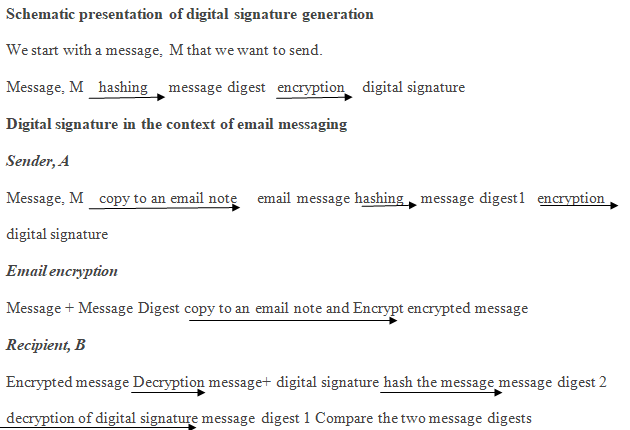
A digital signature is a cryptographically designed code that is attached to an electronic file to verify the authenticity of the sender. Before embarking on the contracting process, the two communicating parties agree on a system of encryption that they will use. They need to protect the data files that they will be exchanging from third party interference. Each of them comes up with a pair of keys known as the public and private keys.
They exchange their respective public keys and keep their private keys secret. When party A wants to send a message to party B, party A runs the original message through a hashing algorithm to produce a message digest. The message digest is then encrypted using B’s public key.
The resulting code is known as the digital signature and is appended to the message which was initially encrypted with B’s public key. On receipt, B uses his private key to decrypt the message obtaining the original message and its message digest. The original message is run through a hashing algorithm and the result is compared with the digest received. If they match, then the integrity of the message is assured.
A digital signature, like a handwritten signature, should be unique for it to be valid. This means that a plainly typed name at the end of a document does not constitute a digital signature. A hacker may intercept the file in transit and formulate his own file, type the name of the genuine sender and send it to the intended recipient. The receiving party will not have a way to verify the source of the file.
On the other hand, a malicious party may intercept the file, make some alterations and resend it posing as the genuine sender. Again, the recipient cannot verify the sender. Such issues are some of the many security issues in the world of e-commerce. If a file that contains instructions to the receiver is altered maliciously, the execution of the resulting instructions will lead to huge losses.
On the other hand, without a legally binding signature, the contract law will be useless. It will be impossible to protect the parties that are getting into an agreement if there will be no prove that the two have actually agreed on such and such terms.
The major importance of a signature is its legal aspect. In business, a signature as seen under the contract law serves to signify commitment to the terms of an agreement. Secondly, it serves to eliminate repudiation (Mattord and Whitman, 2011). However, in e-commerce, a digital signature on its own does not serve as enough evidence.
It must be accompanied by business records as hearsay to substantiate the proof of the signature. The documentation must also be accompanied by a clear explanation from an IT professional involved in data processing and storage throughout the contract period. The person involved must prove what the signatory in question intended when he/she signed the document.
Another issue that arises to challenge the digital signature is the security of the particular contract. He must be able to prove that there is no possibility that the document may have been tampered with after it was signed. If the integrity of the document is questionable, that signature cannot be used as evidence (Mason, 2009; Mattord and Whitman, 2011).
To overcome these challenges and strengthen a digital signature as evidence, it is important to observe the security issues relating to the document. This is possible by applying cryptographic techniques in the generation of signature and in contract storage and transfer.
To achieve this: first, the contract should be transferred and stored in an encrypted format. Secondly, when generating the digital signature, the contract should be used to generate a message digest by hashing. The hash algorithm used can be used to generate the message digest once again in the event that evidence is required in court. If the original hash matches with the new one, then the document’s integrity is valid.
Mason S. (Editor). (2009). Digital Evidence and Electronic Signature Law Review – Volume 6 Pario Communications Limited.
Mattord H., & Whitman, M (2011). Readings & Cases in Information Security: Law & Ethics (1st ed.). Cengage Learning.
Wright, B. (2007). E-Signatures: Are We Building Sufficient Electronic Evidence ? Web.
- RSA: Public/Private Key Encryption
- Reader’s Digest Association’s Strategic Opportunities
- Computer Security and Its Main Goals
- Is Thunderbolt the Real Deal?
- Security in the Information Communication Technology
- Video Game Effects: Good or Bad?
- Adrian Lamo's Hacking: Is It Right?
- Human Computer Interaction – Heptic Technology in PlayMotion
- Chicago (A-D)
- Chicago (N-B)
IvyPanda. (2019, June 18). Digital Signatures in The Business World. https://ivypanda.com/essays/digital-signatures/
"Digital Signatures in The Business World." IvyPanda , 18 June 2019, ivypanda.com/essays/digital-signatures/.
IvyPanda . (2019) 'Digital Signatures in The Business World'. 18 June.
IvyPanda . 2019. "Digital Signatures in The Business World." June 18, 2019. https://ivypanda.com/essays/digital-signatures/.
1. IvyPanda . "Digital Signatures in The Business World." June 18, 2019. https://ivypanda.com/essays/digital-signatures/.
Bibliography
IvyPanda . "Digital Signatures in The Business World." June 18, 2019. https://ivypanda.com/essays/digital-signatures/.
Students connect with cultural history through digital humanities
Asu humanities professor incorporates field into many of her classes.

Photo from Taliesin West field trip in Scottsdale, Arizona. Students worked on field research and collected data to map the desert, sound and noise, using different types of digital mapping software. Courtesy photo
Digital humanities is a field that applies innovative digital tools to traditional humanities disciplines, such as art, literature and history.
In the School of International Letters and Cultures , Serena Ferrando, professor of environmental and Italian humanities, frequently uses digital humanities as the basis for her classes, including ITA 494: City of Water — Uncovering Milan’s Aquatic Geographies, which wrapped up last semester.
Another one of Ferrando’s courses, titled “Noisemakers!”, utilized digital humanities when students embarked on an overnight research trip to Taliesin West . This experience even inspired students to continue this research for their capstone project and honors thesis. Ferrando said the course is very versatile because it combines Italian, environmental humanities and digital humanities.
Digital humanities allows cultural history to be more engaging and accessible to the public through offerings such as virtual tours and other multimedia elements. It is also a powerful tool used for analyzing data and historical records while encouraging collaboration between students of different majors to learn and grow from each other’s expertise.
Many STEM majors, for example, enroll in Ferrando’s courses.
“I want them to, through the process of doing digital humanities, approach humanities-based questions through nontraditional approaches. And to understand that their contribution to questions that are usually discussed in humanities-based courses are absolutely valuable," Ferrando said. "And I also want my humanities-based students to understand that you can also utilize techniques or platforms or tools from STEM fields to explore humanities-based questions. So that's what the whole digital humanities is.”
The cultural conservation of water
The City of Water course expands students' skill set and ability to think critically by using digital methods to examine humanities-based materials, such as photographs, maps, poems, graphic novels, music and historical accounts that are related to the history of the canals in Milan, Italy.
These elements are used by students to create short texts, images, video clips or audio files that reveal the historical layers of Milan’s waterways. They then put this information into a digital map using software like Neatline or Story Maps. The course also gave rise to the Navigli Project, an online exhibit accessible to the public that displays the students' work.
Students gain an array of skills through this project that can be applied to other courses and their professional careers. By creating cultural content through maps of Milan, students learn to think more critically and become proficient in using digital tools and methods to analyze Italian literature, history, philosophy and art as it relates to elements of water.
Students also find parallels between what happened with the canals in Milan and the canals in Phoenix.
“It resonates with the students here because Milan had a lot of water canals until the 1930s. It was a huge network of them, and then they were covered, and now in Milan, you only have two small sections of the canals that are still visible. And the same thing happened here," Ferrando said. "Phoenix was a city of canals and so it's the connection between what happened in Milan, on the other side of the Atlantic Ocean. So there are projects in the digital humanities that actually trace the former canals of Phoenix.”
The waterways in Milan were used for communication and the transportation of goods, but there is so much more cultural history surrounding it. The City of Water course is valuable for students because it teaches them how to work collaboratively while investigating Milan’s literacy, history, and geography as it relates to the canals.
According to the article, "The Navigli Project: A Digital Uncovering of Milan’s Aquatic Waterways," written by Ferrando, the project encourages the cultural conservation of water and water education in Milan.
The class gives students the opportunity to be involved in different social, cultural and political conversations with the people of Milan, with the information they discover and map, despite being an ocean away.
“So what we offer is a conversation with the people in Milan that can be informed with our work. They can actually see what the canals were at the time and so we can be from this part of the ocean, we can be part of conversations about the geographical territory on the other side of the world in Italy,” Ferrando said.
The Navigli Project started eight years ago from the City of Water course. Once the course ended, students wanted to keep mapping the waters of Milan, so Ferrando agreed to continue working with them on an exhibit, now known as the Navigli Project. Each semester, students add what they map to the project if it has yet to be replicated. Ferrando said they probably have over 200 records.
“It was never my intention to create something like that, but it evolved organically from the student's work,” Ferrando said.
Embracing sound via 'Noisemaking!'
Ferrando also uses digital humanities as the basis for ITA 494: Noisemakers! Tracing Origins of Modern Music-Italy. Students examine the acoustic signature of Italy’s musical-literacy history, but the course also challenges students to study the characteristics of their local environment, including Tempe and the ASU campus.
They then create sound maps of their findings using various forms of digital humanities. Some sources could be noise clips, manifestos and scholarly works.
Ferrando became interested in sound technology when taking sound engineering classes at Stanford University for her PhD.
“I just loved all the gear and all the tools that we had in this wonderful recording studio that was available to me at Stanford. And I thought, but I can still utilize this expertise in the academic setting,” she said.
Her ongoing research in this area inspired her to teach courses on noise, such as Noisemakers!, based on the origins of modern Italian music. Ferrando was also interested in noise because it often has a negative connotation, but she wanted to explore its positive sides as well.
One of the highlights of the course was an overnight research trip to Taliesin West, where students worked on field research and collected data to map the desert, sound and noise, using different types of digital mapping software. They created sound walks, a walk focused on listening to the environment.
“For me as an educator and a professor, the most important thing is that students learn how to read around them. They should be able to read the environment. They should be able to read a soundscape," Ferrando said. "And that's the whole purpose of a sound walk, is that very often our hearing is very selective, and our reading is also very selective. And instead, the idea of a sound walk is that you completely open your ears to any type of sound or noise or anything that you might be hearing so you're not selectively listening; you're just hearing.”
One graduate student made a series of podcasts about sound in the environment based on his experience at Taliesin West for their capstone project for the certificate in Digital Humanities. Another student conducted a thesis defense on the subject, creating a digital machine called a Rhythm Harmanzier.
More Arts, humanities and education

Annual symposium to explore fundamentals of trauma-informed education
When it comes to fostering positive and safe classroom communities, teachers are on the front lines every day. And, as society changes, educators increasingly need access to the right tools,…

An ASU-led rare book find
Aaron Pratt began to look through the 1587 copy of "Holinshed’s Chronicles." It was mid-morning, March 1, and Pratt, the Pforzheimer Curator at the University of Texas at Austin's Harry Ransom…

ASU professor named 2024 Teacher of the Year by Southwest Conference on Language Teaching
This year, the Southwest Conference on Language Teaching (SWCOLT) has recognized Arizona State University’s Sara Lee as the 2024 Teacher of the Year. As part of the selection process, Lee gave a…

IMAGES
VIDEO
COMMENTS
This thesis presents a discussion on the electronic signatures and their use in digital documents. This includes an introduction to technological primitives, so- ... Digital signature schemes consist of the following elements:[4] 1. A key generation algorithm that generates a key pair. One is stored as a
Masters' thesis Date 22.06.2021 Number of pages 60 + appendices Abstract . Digital signatures have grown in popularity as a method of signing and collecting signa-tures on documents. After the movement and contact restrictions posed by the corona-virus pan demic in 2020, the popularity of the technology exploded. ...
It can be used for both encryption and digital signature [4, 12]. The security of RSA is based on the difficulty of large prime number decomposition. Because RSA's public key and key are a pair of prime numbers. ... Zhang, R.: Research and application of digital signature. Ph.D. thesis, Shaanxi Normal University (2015) Google Scholar
The digital signature process begins with a. mathematical summary (called a hash code) of the. control. This hash code is a unique fingerprint. identification d igital control. If even a single ...
Gao, L.: Research on digital signature technology based on public key algorithm. Master's thesis, Southwest University of Science and Technology (2018) Google Scholar; 5. Hu, J.: Research and implementation of RSA encryption algorithm. Ph.D. thesis, Anhui University of Technology (2011) Google Scholar; 6.
Since a digital signature is. just a sequence of zeroes and ones, it is. desirable for it to have the following. properties: the signature must be a bit. pattern that depends on the message. being ...
Master's Thesis DIGITAL SIGNATURE: ADOPTION, TECHNOLOGY, COSTS & BENEFITS 17.2.2019 Author: Jenni Lunttila Supervisor / Examiner 1: Mikael Collan ... Author: Title: Faculty: Master's Programme: Year: Master's Thesis: Examiners: Keywords: Jenni Lunttila Digital signature: adoption, technology, costs & benefits LUT School of Business and ...
Experiments showed that digital signatures may evoke a weaker sense of the signer's presence and involvement, and that, accordingly, people perceive the value of electronically signed documents to be lower: job applications are more likely to be discounted and the chance of contract breach is evaluated as higher.
The purpose of this thesis is to study signature schemes whose security relies solely on the security of hash functions; as we previously discussed, quantum adversaries do not greatly a ect the security of hash functions. We give our rst example of a hash-based digital signature scheme in Section2.3.
Digital signatures were rst introduced in the work of Diffie and Hellman, dated back in 1976. It is a scienti c art replacing the traditional way of written signatures. Each signer has a \personal knowledge," or a signing key, to produce ... This thesis mainly concerns with signatures in the latter branch, i.e., the code-based cryptography. It ...
Chapter 8, concludes this thesis. 1.1 Digital Signature Principles. A digital signature associates a digital sequence with an electronic document to represent a handwritten signature on a paper printed document. This digital sequence should be considered similar to a handwritten signature.
Abstract. What is security and what makes a cryptosystem secure? This thesis. explores these questions by looking at the components of a couple public-. key cryptosystems and digital signature schemes, attacks against them, and. ways of improving security.
There are a number of requirements, such as conveyance of information 'in writing', by. a 'document', or authentication of it by 'signature', that have been recognized as barriers to. efficacious e-commerce.3. Writing 'is the preservation and the preserved text on a medium, with the use of signs. or symbols'.4.
company of this thesis, Tieto Oyj, is responsible for B2B intergration and public . 2 sector (Interoperable Financial Administration, 2014.). HAAGA-HELIA University ... digital signature from internet sources, books and journals to sum up all the main findings for the theory part. The second step is to understand about digital signature
1. A Review on Application of Hash Functions and Digital signatures. in the Blockchain Industry. B.A.S. Dilhara. 1 Department of Network & Security, NSBM Green University, Sri Lanka. In a world ...
manipulations, traditional digital signature or w atermarking metho ds cannot b e directly applied. In this thesis, w e rst prop ose robust digital signature metho ds that ha v epro ed to b e useful for suc ht yp es of con ten t authen tication. Also, w e ha v e dev elop ed a no el semi-fragile w atermarking tec hnique to em b ed the prop osed ...
A digital signature associates a digital sequence with an electronic document to represent a handwritten signature on a paper printed document. This computerized succession ought to be viewed as like a ... main results of this thesis, AudunJφsang [11], a senior research scientist with the "Distributed
1 Introduction. A digital signature scheme allows one to "sign" documents in such a way that everyone can verify the validity of authentic signatures, but no one can forge signatures of new documents. The strongest definition of security for a digital signature scheme was put forth by Goldwasser, Micali, and Rivest [17].
The 150-euro customer acquisition cost already has been explained. To evaluate the value of the extra trading days (an average of 13 in the estimation), the euro value per year of a customer must be known, which here is estimated at 100 euro. This gives an implied value of 3.56 euro per customer in added trading time.
A digital (electronic) signature is - like a regular signature on a piece of paper - a method for identification (of the person who wrote the document) or authenticity (so that the recipient of a signed document can be sure of who signed the document). ... Digitise your old thesis; Read more about Digital Signatures at Medarbetarportalen ...
Table of Contents List of Figures . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . vii List of Tables ...
Digital Signature is a mathematical scheme which ensures the privacy of conversation, integrity of data, authenticity of digital message/sender and non-repudiation of sender. Digital Signature is embedded in some hardware device or also exits as a file on a storage device. Digital Signature are signed by third party some certifying authority.
Digital signatures are a type of electronic signature that offers extra protection. They use the public key infrastructure (PKI) to verify the signer's identity and the signed document's integrity. A digital signature uses cryptography to bind the individual who signed to the record, rendering it tamper-proof.
In this paper, the legal issues of digital signatures will be discussed. A digital signature is a cryptographically designed code that is attached to an electronic file to verify the authenticity of the sender. Before embarking on the contracting process, the two communicating parties agree on a system of encryption that they will use.
digital signature: A digital signature (not to be confused with a digital certificate ) is a mathematical technique used to validate the authenticity and integrity of a message, software or digital document.
Digital humanities is a field that applies innovative digital tools to traditional humanities disciplines, such as art, literature and history. In the School of International Letters and Cultures, Serena Ferrando, professor of environmental and Italian humanities, frequently uses digital humanities as the basis for her classes, including ITA 494: City of Water — Uncovering Milan's Aquatic ...