pfSense router-on-a-stick VLAN configuration with a Cisco SG300
Last revised 28 january 2018., introduction, cisco sg300, initial connection, general configuration, create vlan ids, configure interfaces.
- Assign switch IP
- Power saving notes
My pfSense baseline guide makes extensive use of VLANs to provide enough network segments to facilitate the segregation of devices into the following categories
Without VLANs it would be tough to provide enough network interface connections to enable me to apply strict firewall rules and traffic prioritisation to support my needs. For example, the video surveillance system is confined to a single VLAN and has very limited abilities to communicate with devices in other subnets and the internet, my gaming consoles have prioritisation to ensure smooth and problem free network play. These Virtual LAN (VLAN) segments are connected back to pfSense in a ‘router-on-a-stick’ configuration. Its referred to as ‘router-on-a-stick’ because of the single trunk cable connecting the 802.1Q capable switch to our pfSense router. This enables our switch to handle local subnet traffic switching whilst leveraging pfSense to firewall inter-subnet traffic. Some of my fileservers and devices generate a substantial amount of traffic and not having to push all this traffic through pfSense allows it to better handle the load it does need to process.
Here’s a diagram to help illustrate my configuration.
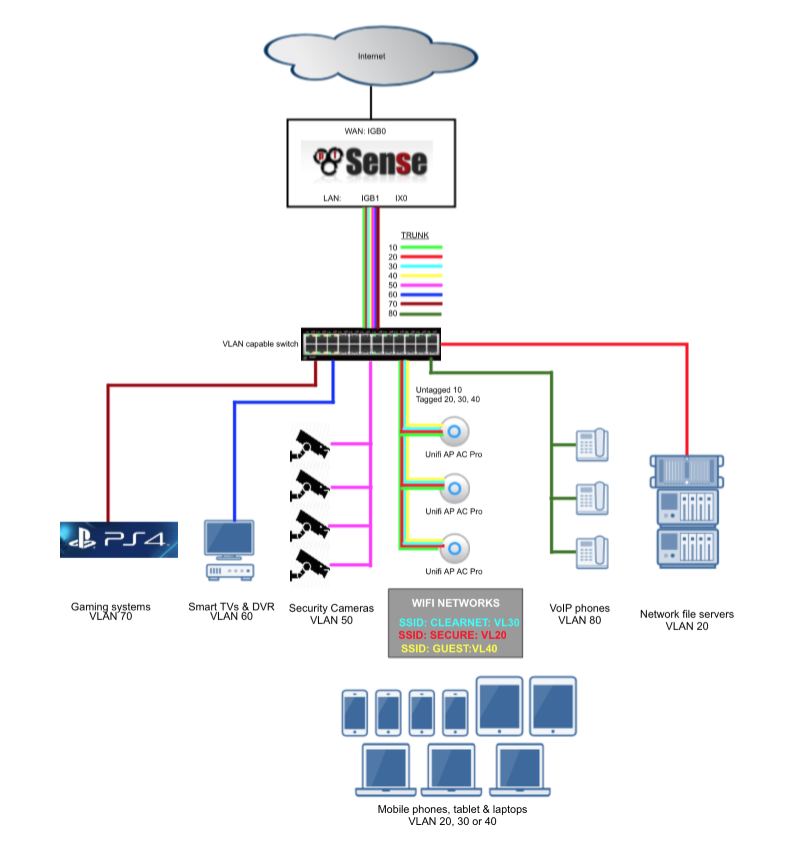
The Cisco SG300 switch is an affordable, high-performance, relatively easy to manage device that’s designed specifically for smaller homes and businesses whilst retaining many of the advanced feature sets of other enterprise level products. Although this guide is created on a SG300-10PP which offers fanless operation, 10 gigabit ethernet ports and supports power over ethernet (PoE) the SG300 range includes models with up to 48 ports. The Cisco SG500 range offer a similar configuration interface and also includes 10 gigabit networking ports on certain models suitable for those needing higher bandwidth capabilities.
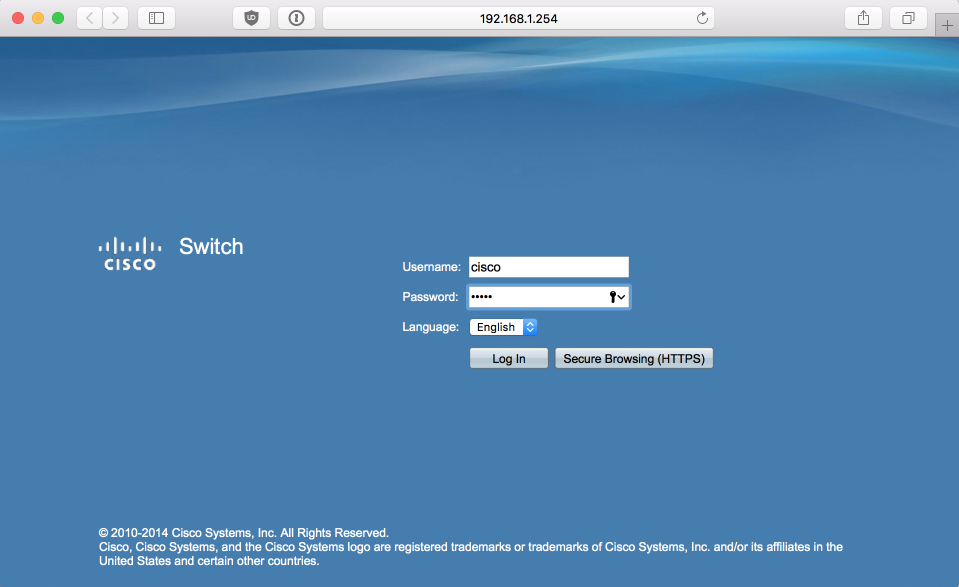
The SG300’s configuration page by default is available on the 192.168.1.254 address. To access it set your PC that you will be using to configure it from into the 192.168.1.x address range, I used 192.168.1.100. Connect your PC to the SG300’s port 8. You could use another but this keeps the lower ports free and avoids unnecessary complications further on in this guide. Connect the power and wait for the SG300 to complete its boot process, its takes a little while before you can access the login page at http://192.168.1.254 Login with the default username cisco and password cisco
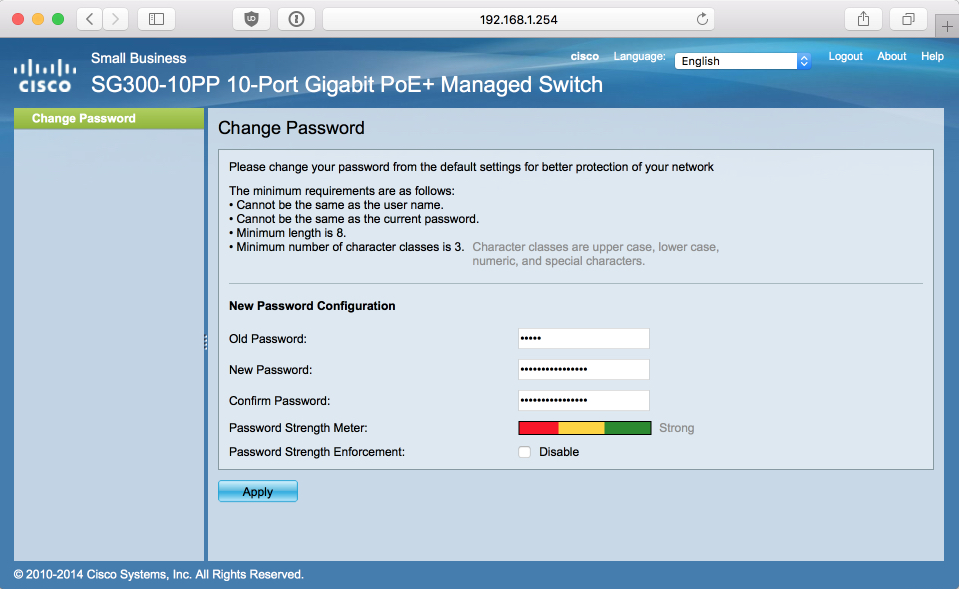
When you log in you will be initially prompted to change the default password, set it to something secure.

Enable L3 routing
Enabling layer3 routing will enable us to assign an IP address to our VLAN(s) and ease access post configuration easier. Changing the fundamental processing mode will reset the switch back to its default state.
Navigate to Administration > System Settings and set
- Host name = sg300
- System Mode = L3
Click Apply which will reboot and reset the switch. Once the switch has booted, log back in with default username (cisco) and password (cisco) again where you will be prompted to set your secure password again.
Save & Apply
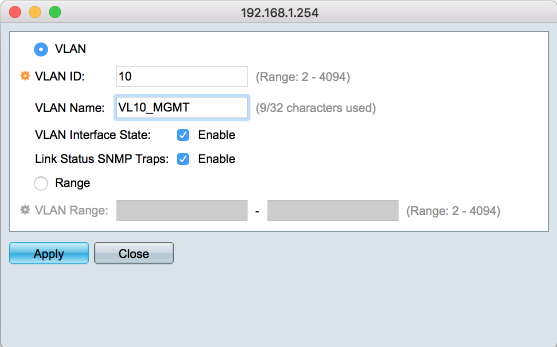
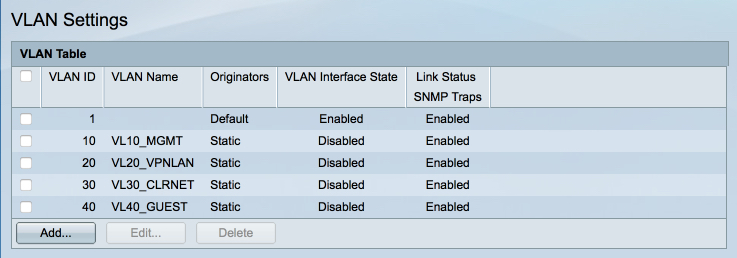
Navigate to VLAN Management > VLAN Settings, we will configure the VLAN IDs here required to support my baseline guide. I’ve added some images to help illustrate configuration options and final states.
Create VL10_MGMT ID
- VLAN ID: 10
- VLAN Name: VL10_MGMT
- VLAN Interface State: Enabled
- Link Status SNMP Traps: Enabled
- Range: [ ] Click Apply
Create VL20_VPNLAN ID
- VLAN ID: 20
- VLAN Name: VL20_VPNLAN
Create VL30_CLRNET ID
- VLAN ID: 30
- VLAN Name: VL30_CLRNET
Create VL40_GUEST ID
- VLAN ID: 40
- VLAN Name: VL40_GUEST
- Range: [ ] Click Apply and then Close
When you are done, your VLAN ID table should look like this
I recommend saving your configuration at this point which is made available through he flashing Save prompt in the top menu bar. Anytime I mention to save I refer to saving the current state to the running and startup configurations.
In this guide we will create the following interfaces:
Broadly thinking an access mode port can be part of only one VLAN and is typically used to connect to a device or PC. A trunk mode port can be part of one or more VLANs and is typically used to carry information between switches or devices.
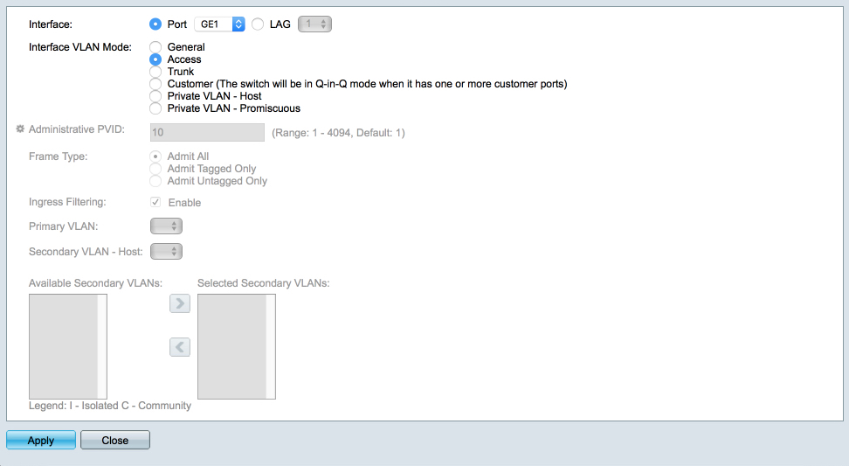
Setup VL10_MGMT access port
Navigate to VLAN Management > Interface Settings
Highlight GE1 and select Edit
- Select ‘Access’ Apply & Close
Navigate to VLAN Management > Port VLAN Membership
Highlight GE1 and select ‘Join VLAN’
- Remove ‘1UP’ (highlight it, and click the left arrow)
- Add ‘10’ as Untagged. (highlight it, and click the right arrow)
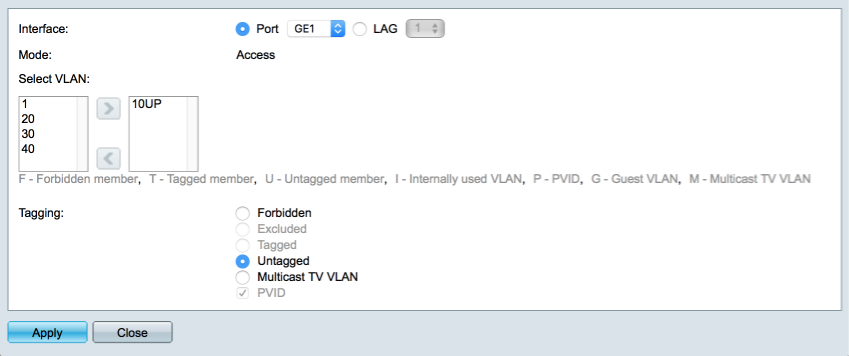
Click on Apply and Close

VL20_VPNLAN access port
Highlight GE2 and select Edit
Highlight GE2 and select ‘Join VLAN’
- Remove ‘1UP’
- Add ‘20’ as Untagged. Click on Apply and Close
VL30_CLRNET access port
Highlight GE3 and select Edit
Highlight GE3 and select ‘Join VLAN’
- Add ‘30’ as Untagged. Click on Apply and Close
VL40_GUEST access port
Highlight GE4 and select Edit
Highlight GE4 and select ‘Join VLAN’
- Add ‘40’ as Untagged. Click on Apply and Close
Trunk to Unifi AP
The trunk needs to be configured to provide the management interface on the untagged traffic, and the other SSIDs on tagged packets.
Verify GE5 is configured as a trunk port
Highlight GE5 and select ‘Join VLAN’
- Add ‘10’ as Untagged.
- Add 20, 30 & 40 as tagged Click on Apply and Close
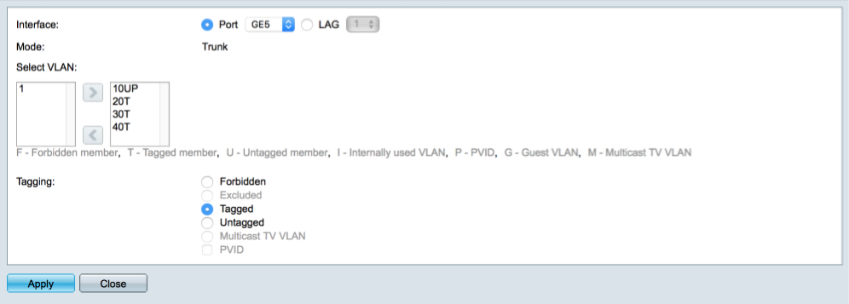
Trunk to pfSense
The trunk needs to carry all the VLANs between our switch and pfSense’s parent interface in tagged packets.
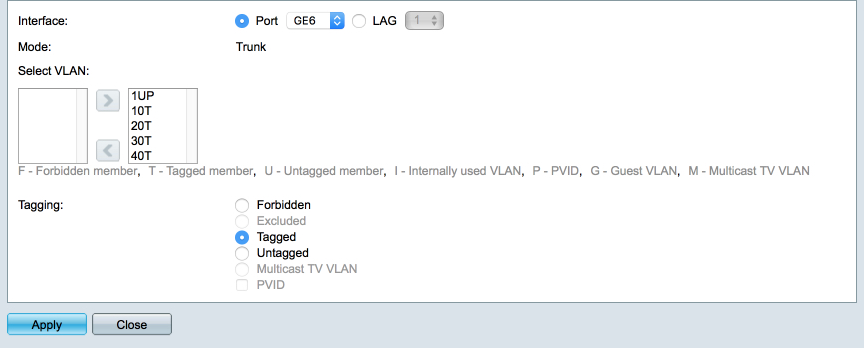
Verify GE6 is configured as a trunk port
Highlight GE6 and select ‘Join VLAN’
- Leave 1UP present
- Add 10, 20, 30 & 40 as tagged Click on Apply and Close
When you are complete you Port LAN configuration should look like this
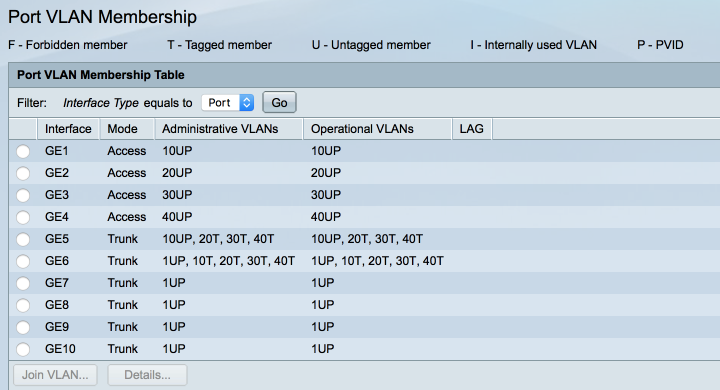
Save the current configuration to the running and startup configurations.
Connect a Cat5e cable between your pfSense trunk interface and port 6 on the SG300 switch.
Assign switch IP address
We will now assign a fixed IP address to our switch via the VL10_MGMT VLAN to enable us to modify the configuration as and when needed.
Navigate to IP Configuration > IPv4 Interfaces
- Select VLAN 10
- Select Dynamic IP address Click Apply
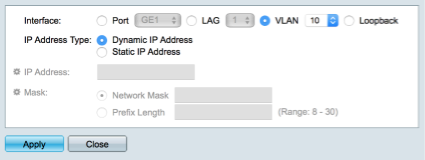
Don;t worry at this point you will lose contact with the SG300. Setting the IP address of the VL10_MGMT interface overrides the default 192.168.1.254 address we have been using so far. Before we can reconnect, we will configure pfSense to provide a fixed IP address via a Mac address reservation. I like to assign fixed IP addresses to my infrastructure hardware and I prefer to do it through Mac reservations within pfSense. This has a benefit of maintaining accurate routing tables and provides me with a centralised resource to keep track of current reservations.
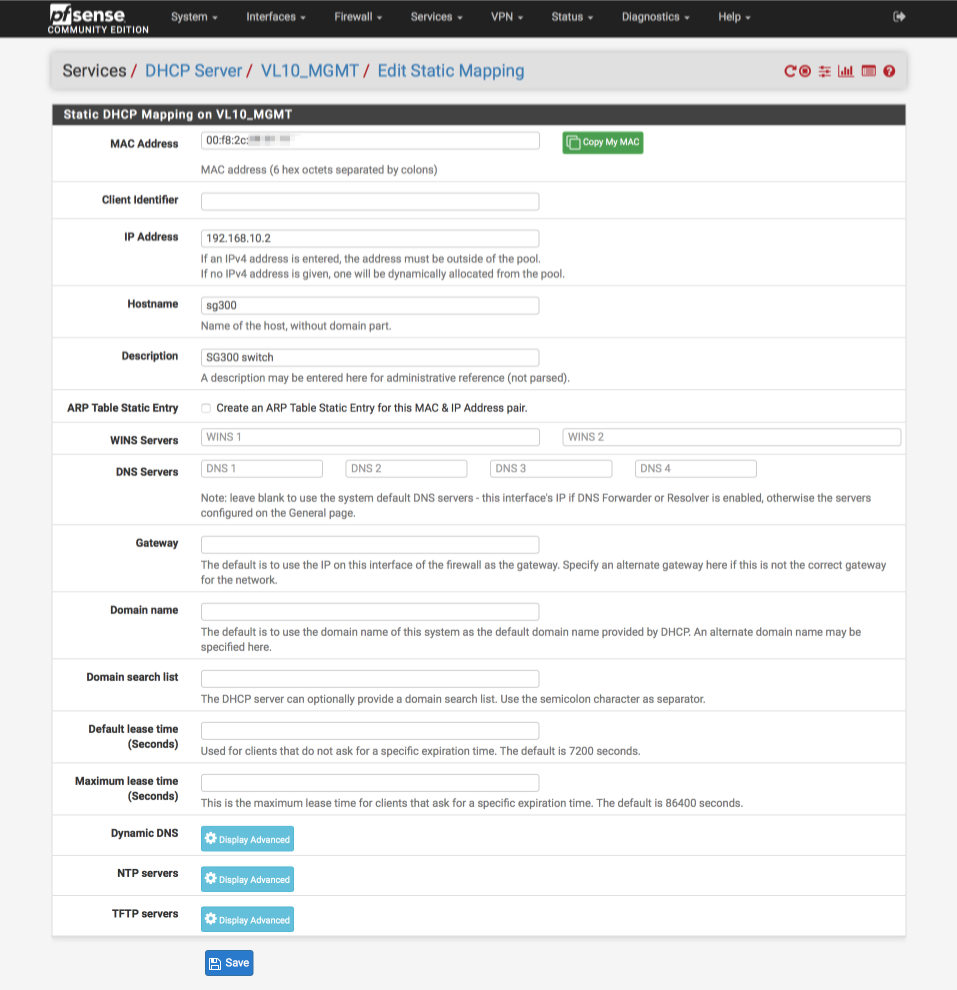
Log into pfSense and navigate to Statistics > DHCP reservations where you will hopefully see our current SG300 IP address assignment as made by the DHCP server, in the example below you can see the SG300 has acquired the 192.168.10.162 address.
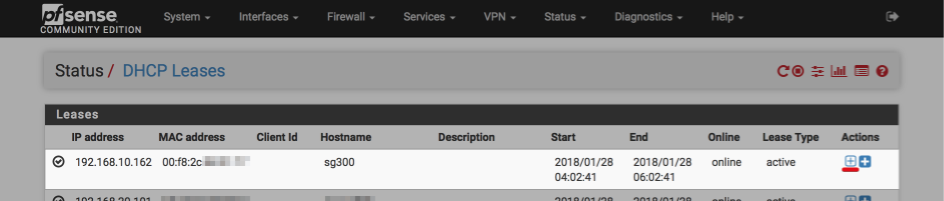
Click the ‘plus’ symbol (underlined with red above) to assign a static IP address, I’m using 192.168.10.2.
Its now worth rebooting your SG300 switch to ensure it picks up the new IP address we just allocated for it.
Disconnect your PC from the SG300 switch and reconfigure it to obtain an IP by DHCP.
Connect your PC to port 1 and assuming everything has worked you should be awarded an address in the VL10_MGMT subnet of 192.168. 10 .x.
Verify ports 2 provides an address in VL20_VPNLAN range, i.e 192.168. 20 .x Verify ports 3 provides an address in VL30_CLRNET range, i.e 192.168. 30 .x Verify ports 4 provides an address in VL40_GUEST range, i.e 192.168. 40 .x
Connect your Unifi AP to SG300’s port 5 and verify you can connect to each SSID and are awarded a corresponding IP address.
Verify you can access the SG300 web configuration page at 192.168.10.2 from VL10_MGMT, VL20_VPNLAN & VL30_CLRNET. You should no able to access it from VL40_GUEST due to our pfSense firewall configuration blocking access to other internal networks.
Configuration notes
Power saving mode.
The Cisco SG300-10PP is equipped with some useful power saving technology but I have previously found some issues with PoE being enabled with certain devices. If you find you are having problems try disabling the power saving features to eliminate this possibility.
To disable navigate to Port management > Green Ethernet > Properties and set
- 802.3 Energy Efficient Ethernet (EEE) = Disabled Apply
SG300 manual

IMAGES
VIDEO
COMMENTS
Step 1. Log in to the web configuration utility and choose VLAN Management > Interface Settings. The Interface Settings page opens: Step 2. Chose an interface from the Interface Type drop-down list and then click Go. Port — A single physical port on the switch. LAG — A group of ports used to increase link reliability.
How to Configure Interface Settings on the SG550X-24 (active) Step 1. Navigate to VLAN Management > Interface Settings. Step 2. Select a Global Ethertype Tagging method. The options are: Dot1q-8100 — Also known as IEEE 802.1Q. It is the standard for tagging frames on a trunk and supports up to 4096 VLANs.
Step 2. Click Add to assign IP address for VLANs. Step 3. Check VLAN and select VLAN ID number from the drop down menu. Step 4. Assign IP address for the VLANs. • IP Address Type — How IP address will be assigned. - Dynamic IP Address — DHCP dynamic IP address assignment. - Static IP address — Manually configured IP address assignment.
The next steps explain how to assign ports to VLANs on the 200/300 Series Managed Switches. Step 1. Log in to the web configuration utility and choose VLAN Management > Port to VLAN. The Port to VLAN page opens: Step 2. In the Filter field, from the VLAN ID Equals To drop-down list, choose the appropriate VLAN. Step 3.
Configuring Dynamic Access Ports on a VMPS Client. To configure a dynamic access port on a VMPS client switch, perform this task: Enters global configuration mode. Enters interface configuration mode and specifies the port to be configured. Sets the port to access mode. Configures the port as eligible for dynamic VLAN access.
Hi Guys, I am attempting to set up dynamic VLAN assignment using a Cisco SG300 switch and a Windows NPS server. This is my first time trying this. All appears to be working and test clients are being authenticated howe… Hi Guys, I am attempting to set up dynamic VLAN assignment using a Cisco SG300 switch and a Windows NPS server. ...
Supports time-based 802.1X Dynamic VLAN assignment . Web Based Authentication. Web based authentication provides network admission control through web browser to any host devices and operating systems. STP Bridge Protocol Data Unit (BPDU) Guard. A security mechanism to protect the network from invalid configurations.
This document describes the concept of dynamic VLAN assignment and how to configure wireless LAN controller (WLC) and a RADIUS server to assign a wireless LAN (WLAN) clients to a specific VLAN dynamically. In this document, the RADIUS server is an Access Control Server (ACS) that runs Cisco Secure Access Control System Version 5.2.oduction
jkintz79 (JKintz79) July 30, 2014, 4:42pm 1. So I usually don't touch these low-end "Cisco-ish" switches, but need to figure out if I can get DVA configured without the need for a RADIUS server. Basically I want to punch in a list of MAC addresses into the switch, and tell it to drop these clients into VLAN## if the switch sees the MAC ...
Step 1. Log into to the web configuration utility and choose VLAN Management > Voice VLAN > Properties. The Properties page opens: Step 2. In the Voice VLAN ID field, enter a VLAN ID assigned to the Voice VLAN. Note: The VLAN ID cannot be the default VLAN but can be a range. Step 3.
Go to the user1's Edit page. From the User Edit page, scroll down to the Cisco Airespace RADIUS Attributes section. Check the check box next to the Aire−Interface−Name attribute and specify the name of the dynamic interface to be assigned upon successful user authentication. This example assigns the user to admin VLAN.
In this lab, we will configure the following:1- Create and modify VLAN2- Assign static IP address to VLAN interface 3- Create Trunk on port4- Assign new Nati...
Dynamic VLAN Membership Overview. When a port is configured as "dynamic," it receives VLAN information based on the MAC-address that is on the port. The VLAN is not statically assigned to the port; it is dynamically acquired from the VMPS based on the MAC-address on the port. A dynamic port can belong to one VLAN only.
Connect a Cat5e cable between your pfSense trunk interface and port 6 on the SG300 switch. Assign switch IP address. We will now assign a fixed IP address to our switch via the VL10_MGMT VLAN to enable us to modify the configuration as and when needed. Navigate to IP Configuration > IPv4 Interfaces. Click Add. Select VLAN 10; Select Dynamic IP ...
Configure internal users on Cisco ISE Step 3. Configure the RADIUS (IETF) attributes used for dynamic VLAN Assignment Configure the Switch for Multiple VLANs Catalyst 9800 WLC Configuration Step 1. Configure the WLC with the Details of the Authentication Server Step 2. Configure the VLANs Step 3. Configure the WLANs (SSID) Step 4.
Dynamic VLAN assignment is one such feature that places a wireless user into a specific VLAN based on the credentials supplied by the user. This task to assign users to a specific VLAN is handled by a RADIUS authentication server, such as Cisco ISE. This can be used, for example, in order to allow the wireless host